Identosphere 108 • Passwords are Expensive • Save 20.3M • Contribute to our Patreon! • Decentralized Semantics WG Launch
You weekly guide to the latest news events and related info surrounding development and implementation of decentralized identity and verifiable credentials
Welcome to Identosphere Weekly Digest!
Consider pledging a small amount each month via Patreon …or via Paypal or a one time contribution with year end budget
Read previous issues and Subscribe : newsletter.identosphere.net
Content Submissions: newsletter [at] identosphere [dot] net
Upcoming
EEMA Open SSI Forum 11/17 Berlin
[notssi] Sovereign Identity Crisis: State, Self, and Collective in a Digital Age - November 17, 2022 - Temple iLIT Nov 17
eSSIF-Lab final event 12/1 Brussels (Kaliya will be there)
Thoughtful Biometrics Workshop 2/13-17 [Registration]
IIW 36 April 18-20, Mountain View
VC <> mDL Project Stakeholder Interviews IdentityWoman
On September 12, 2022, Identity Woman in Business announced a community project “Where the W3C VCs meets the ISO 18013–5 mDL” sponsored by Spruce to help:
Enable a bigger ecosystem of players to take advantage of mobile driving licenses by making sure the VCs are a viable alternative for implementers to the ISO 18013–5 standard, and are compatible to the fullest extent possible of the outputs of ISO working groups
Give both VC and mDL wallet vendors equal opportunity to compete and provide users with options by urging the open-up of privileged, internal APIs for all wallet vendors and developers.
Following the announcement, we hosted the first community session on September 27, answering questions about the project, understanding relevant existing efforts and gathering initial input for the project deliverables.
Hiring
Open position: Researcher Apply by 12/5
with a background in governance, human-centric infrastructures, and data ecosystems.
Explainer
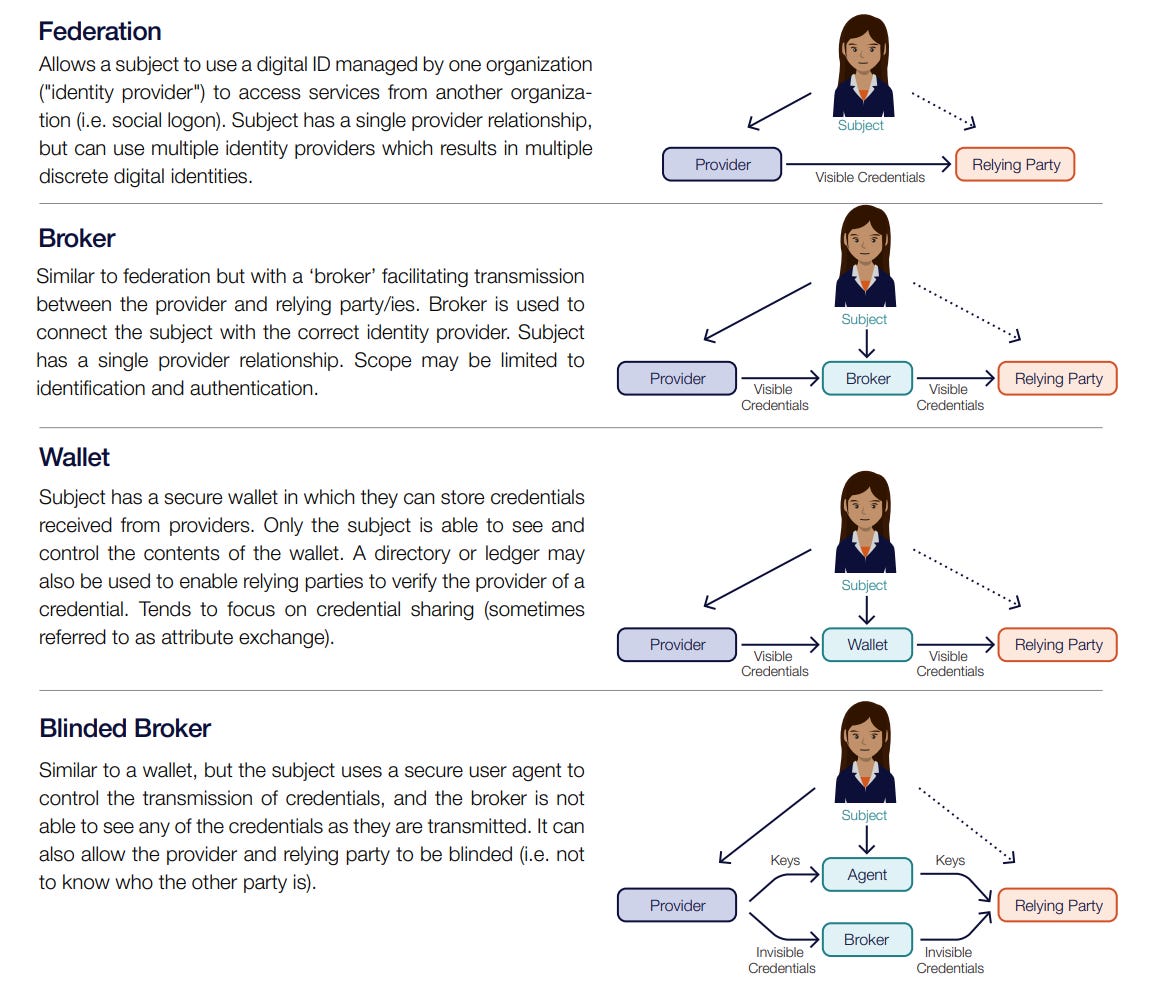
Making Sense of Identity Networks DIACC [Paper][Summary]
* not new, but good
This DIACC white paper offers an unbiased and objective evaluation of identification networks and is based on research done by DIACC member Consult Hyperion. It was created in conjunction with DIACC through a community review process. The paper presents a high-level framework with which to comprehend and evaluate the many kinds of identity networks that now exist or are being developed, using "Mary" as an example. It also provides advice to people who are thinking about joining such a network.
Transmute Tech School 101: Linked Data Enables Integration Across Systems transmute
Understanding Distributed Identity Management Systems Metadium
we'll discuss the advantages of adopting blockchain as well as how it might be applied to identity management systems.
AnonCreds: Anonymous Credentials Stephen Curran, Northern Block
• Can the way that W3C credentials are formatted get in the way of interoperability in the future?
• Are there use cases where AnonCreds aren’t the right implementation?
• Are AnonCreds more computing intensive than W3C credentials?
• Future for AnonCreds and for Hyperledger Indy
• Why Revocation remains the weak point of AnonCreds and Indy
• Is mDL better suited than AnonCreds for Driver’s Licence use cases?
Business
Financial services still use passwords – and it’s costing them Puja Sharma, FIDO Alliance
[survey results] Post-pandemic security: 79% IT decision-makers want company password manager implemented FIDO Alliance
Standards Work
Launch of "Decentralized Semantics Working Group" Invitation Paul Knowles, Human Colossus Foundation
Decentralized Semantics is a state-of-the-art new data discipline being driven by the Foundation to enable accurate morphological, semantical, and pragmatic structuring of unstructured data. It drives the development of technologies for the DDE Semantic Layer and provides the essential framework for the Dynamic Data Economy (DDE) that we foresee (Layer 1 of the DDE Trust Infrastructure). One of the first tools we created for the Semantic Layer is the recently released OCA, an architecture for capturing the metadata necessary to analyze and preserve the meaning of inputted data.
[thread] cheqd.io @cheqd_io
This means that an implementer can utilize Verifiable Credentials (VCs), Open ID Connect, DIDComm, Credential Handler API, or any other transport envelope to transmit JSON Web Tokens (#JWTs), VCs, JWT-VCs, or any other JSON Claimformat.
[Issue] Make the usage of @context optional #947 vc-data-model
The use of @context has been considered as being optional. As the use of @context is needed in both JSON and JSON-LD, this would be a normative modification to the present specification. This topic is to discuss if this is a good concept and the possible mechanism(s) to carry it out.
Development
Five Ruby Gems for Authentication and Authorization Carla Urrea Stabile, Auth0
Find out how to utilize each of the five different Ruby gems for authentication and permission.
Do You Need a Blockchain to Build Your IDtech Product? Trinsic
The decentralized identity infrastructure provided by Trinsic's next-generation platform is unrelated to any one particular ledger. This may come as a surprise in the realm of decentralized identification, but it's actually a significant win for product developers. We'll delve into a couple of the causes of Trinsic's ledger-less default in this piece.
[thread] We choose the "Envelope" as the central metaphor for our Smart Documents @ChristopherA, Blockchain Commons
“intriguing method for resolving DIDComm-related issues. I like how this is concentrating on use cases like key recovery” KyleDH
securely store and transport certificates, plain text, encrypted text, tiny or big amounts of data, and much more!
Trust Registries
[research literature] Bottom-up Trust Registry in Self Sovereign Identity Kai Jun Eer, Jesus Diaz, Markulf Kohlweiss: Edinburgh University, IOHK
we suggest a trust registry design that addresses the issue of people's confidence in their own identities. We also implement a trust registry incentive system to encourage active and truthful participation from all stakeholders.
Product Passports & Trust Registry Solutions Continuum Loop
There are several potential applications for digital product passports in sectors like transportation, forestry, mining, energy, and healthcare. This article presents several actual instances of trust registries and digital product passports
Interop
Paving the way towards human-centric data spaces MyData
One of the cornerstones of the European strategy for data is the concept of data spaces that should become EU-wide and interoperable. To support this vision to become a reality, European Commission is setting up the Data Spaces Support Centre (DSSC) through an EU-funded multi-year project.
Wallets
Your data available at any time with the Lissi Wallet backup lissi
This article explains what the Lissi Wallet backup is and how to utilize it to recover it in the event of a loss.
Data Talks
What is Decentralized Self Sovereign Data Irene Ng, Hub of All Things
This blog article explains decentralized self-sovereign data, which was briefly mentioned in the IFC-hosted session on "Distributed Data Ecosystems: Heterodox Approaches to Data Portability" during the Singapore FinTech Festival on November 4, 2022. Let's start with a fundamental grasp of data's economic property. A "non rivalrous" good, that is.
[Podcast] E14 - Whitehall IDM London / AI+ML & Automation / IGA / Machine Identity / Identity Business Cases / Identity for Zero Trust This week in Identity
A variety of subjects, case studies, and vendor presentations were covered during this one-day event. When it comes to the rise of AI+ML in authentication and IGA, Simon and David pick out the best and most intriguing aspects, while posing the question: Is identity turning into a big data issue?
The quest for accurate data (Part 1): “Integrity” versus “Authenticity.” Human Colossus Foundation
The cryptographic data security qualities "Integrity" and "Authenticity" guarantee data accuracy through a digital network, link, or exchange. Unfortunately, only sometimes are both characteristics followed concurrently, which compromises security.
Use Case
[youtube] Why we need self-sovereign identity to enable the Internet of Things BC4EU Summit 2022
Our presenters in this panel discussion covered the specifics, requirements, and possible implementations for ensuring self-sovereign identification in order to enable the Internet of Things.
Blockchain and Health Care: BurstIQ Use Cases That Leverage Verifiable Credentials Dock
Verifiable Credentials are critical in blockchain and healthcare, as shown by these three BurstIQ use cases. To make their health data portable and secure, BurstIQ adopted our Verifiable Credential technology.
What Could Your Organization Do With $20 Million? Deborah Mcginn, Radiant Logic
$20.3M in total savings over three years
239% ROI and payback within six months
$9.2M technical debt reduction
25% reduction in the risk of data breaches
80% operational efficiency boost
Password-based attacks spike in prevalence SC Media
90% of the compromised accounts lacked "strong authentication," which stands for the absence of multi-factor authentication, according to Microsoft's Digital Defense Report 2022.
[report] A win/win/win: the self-sovereign identity opportunity for travel Phocuswright
Promising to dramatically improve the trust in internet identity for all parties - people, organizations and even things can now have a trusted and provable digital identity according to Phocuswright’s latest research report on the technology Self-Sovereign Identity: Unlocking Seamless Travel.
[research literature] Technical Design and Development of a Self-Sovereign Identity Management Platform for Patient-Centric Healthcare Using Blockchain Technology Blockchain Healthcare Today
MediLinker allows users to store their personal data on digital wallets, which they control. It uses decentralized trusted identity using Hyperledger Indy and Hyperledger Aries.
Company News
[Interview] David Chadwick CEO Verifiable Credentials Ltd NGI eSSIF-LAB
Since the education market is one of CCP’s identified markets for verifiable credentials, CCP’s short-term goal is to successfully participate in the JFF Plugfests in order to show that Identiproof is a standards conformant product that can interwork with a whole range of different verifiable credential products from different providers across the globe.
Announcing the Launch of Our New Website! Transmute
[tweet] Walt.id @walt_id · Nov 11
Wallet Connect complies with SSI We won the #ETHLisbon Hackathon by adding #SSI (exchange of #W3C Verifiable Credentials) to the @WalletConnect V2 protocol stack. [Demo][Slides]
Organization
Welcoming Sparkasse Bank and Diligencia to the LEI Everywhere Program Steve Waite
Sparkasse Bank Malta Ltd and UK-based Diligencia are the two new Validation Agents inside the Global LEI System that the GLEIF announced today.
Twitter Buyout
Verifying Twitter Phil Windley - A verified credential-based approach would be preferred to ensure user authenticity without compromising privacy.
Musk lays off Twitter Mexico staff. The government rejoices Daniela Dib, Rest of World
Decentralized web
Mastodon Is Just Blogs Simon Willison
Social Media on the Decentralized Web Filecoin Foundation
[corrected] Bluesky Social, The decentralized Twitter-Killer, By Jack Dorsey Sylvain Saurel
[YTPlaylist] IPFS 201: App Design Patterns and Developer Tools IPFS Camp
State of the IPFS DevTools ecosystem Brendan O'Brien, Brooklyn Zelenka, Carson Farmer & Sara Feenan
What is IPLD Anyway? Mauve Signweaver - IPLD is data that is content addressed and is linked. The main detail is the IPLD model, which is an abstract specification for many types or kinds of data that can be represented as well as exchanged in the system.
Bluesky and IPLD Jay Graber - Bluesky is an AT Protocol, a new social networking foundation that allows creators freedom from platform constraints, developers the ability to build, and users control over their experience.
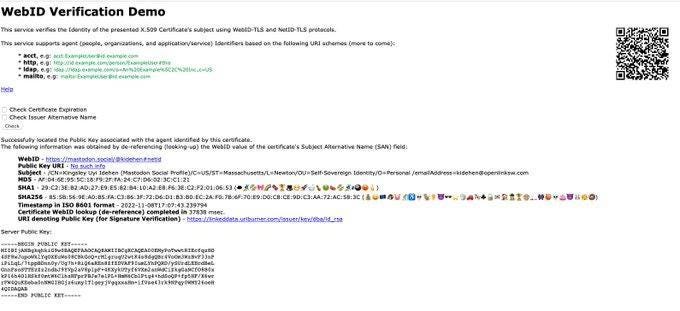
[tweet] Kingsley Uyi Idehen @kidehen Nov 8
using another one of my @joinmastodon profile pages as the credentials store reconciled to signed credentials in my local X509 certificate -- as part of an extended TLS-handshake. https://linkeddata.uriburner.com/ods/webid_demo.html
Thanks for Reading!
Read more \ Subscribe: newsletter.identosphere.net
Support this publication: patreon.com/identosphere
Contact \ Submission: newsletter [at] identosphere [dot] net