Identosphere 164 Feb 1-13: China RealDID • Nepal gets $50m for Credential Lockers • Vietnam Edu Creds • DigiYatra Passport Enrollment • Singapore <-> India Edu Creds • Kyndryl Joins DIF
This is the mostly weekly Identosphere Newsletter sharing highlights from around the web covering Decentralized and Self-Sovereign Identity curated by Kaliya Young, Identity Woman.
Upcoming
Human Agency Summit, February 23, Napa Valley (Kaliya will be there along with many other decentralize identity folks)
DIF Unconference Africa (an IIW Regional Event) Feb 24-26, 2026 Cape Town
KERICONF26 April 21-23 2026, Lehi, Utah (US)
Internet Identity Workshop #42, April 28-30, 2026, Mountain View California
Agentic Internet Workshop #2, May 1, 2026, Mountain View California
dice: Digital Identity unConfernece Europe (an IIW Regional Event) June 22-24, Copenhagen, Denmark
New W3C Community Group
Proposed Group: Physical Asset Attestation (UORA) Community Group
The mission of the Universal Object & Resource Attestation (UORA) Community Group is to develop a vendor-neutral, decentralized protocol for the identity, state verification, and lifecycle tracking of physical assets. By bridging the gap between physical objects and digital identifiers, UORA enables every resource to function as a first-class citizen of the internet, fostering global trust, transparency, and interoperability across supply chains and industries.
Are We Worried Yet Department
How AI Surveillance Tech is Creeping From the Southern Border Into the Rest of the Country
Last week, The New York Times reported that when a U.S. citizen in Minneapolis was following ICE agents to observe their conduct, one agent addressed her by name — information the agent may have obtained using some kind of facial recognition system, though DHS would not specify whether that was the case or which technology ICE is using. And while there’s something chilling about government agents generating a correct identification this way, the technology is also prone to false positives and errors, and according to reporting by WIRED, is being used by DHS for identity “verification” tasks it wasn’t designed for.
(Doc Searls) Because Pricing is Getting Too Personal
Surveillance pricing already has its own page in Wikipedia. It also has its own authority: Abbey Stemler, Associate Professor of Business Law and Ethics and Weimer Faculty Fellow in Business Law & Ethics at Indiana University’s Kelly School of Business. And she’ll be speaking about her work a week from now: February 19, 2026 4-5 ET
(Evercred) Digital Police Identity Verification in India: Combatting the “Digital Arrest” Crisis
The transition to digital policing tools in India has outpaced the development of secure identity infrastructure. The new Bharatiya Nyaya Sanhita (BNS) allows for the service of electronic summons. This is a necessary step towards modernization. However, legal experts highlight a critical gap: there is no current statutory mandate for how these electronic interactions must be authenticated.
[Research] Important Self-sovereign identity: A conceptual framework and research agenda
Self-sovereign identity (SSI) is a novel approach to digital identity management, which is controversially discussed in technological communities and academia and lately also in the political space. Positions in the debate range from touting SSI as introducing a paradigm shift in internet identity and user privacy, while others dismiss the concept as libertarian hyperbole. SSI aims to give individuals an independent digital existence and control over their digital identities. Technically, this is achieved by providing individuals with digital identity wallet applications, which allow them to store and present digitally verifiable credentials. Despite its transformative potential, SSI is not comprehensively conceptualized in information system research. Therefore, in this Fundamentals article, we offer the following contributions: First, based on existing information systems research, we provide a consolidated definition and a conceptual framework of SSI structured along five analytic levels: (1) foundational principles, (2) credential exchange, (3) technical building blocks, (4) applications, and (5) governance. Second, we present an information systems research agenda on SSI, including concrete research questions and promising theoretical directions.
World Bank Backs Nepal Digital Transformation with $50M and Verifiable Credentials Locker
The World Bank has approved $50 million in financing for the Nepal Digital Transformation Project, an initiative aimed at expanding the country’s digital public infrastructure and accelerating the digitization of public services.
The Major Digital Trust Trends Shaping Asia in 2026
Trend 2: The rise of decentralized identity
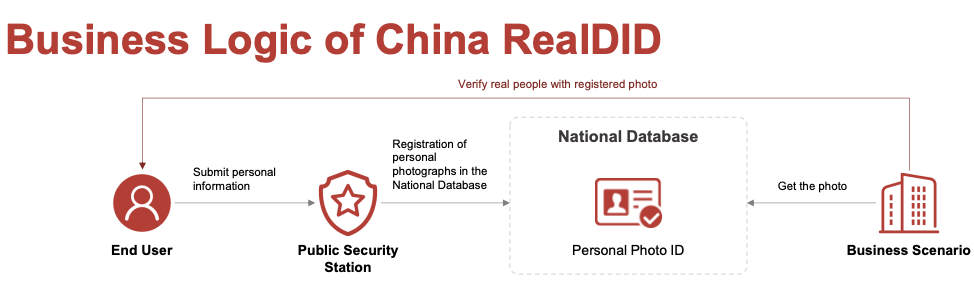
China’s RealDID system, for example, uses decentralized identity blockchain infrastructure to allow credentials to be verified without being repeatedly shared.
In Hong Kong, for example, the DID system was used in a limited pilot to allow visitors from mainland China to register for regulated stablecoin services without giving away any of their personal details.
In many APAC jurisdictions, there is no clear statutory recognition of self‑sovereign credentials, and AML/KYC laws still assume the use of centralized government ID systems. Enterprises tend to move cautiously when infrastructure lacks clear standards or legal recognition.
[slide deck] Introduction of China RealDID System
Luvia and Open Campus partner to bring verifiable credentials to Vietnamese students through initiative supported by Ministry of Education and Training
Hanoi, Vietnam - Luvia and Open Campus have announced a strategic partnership to provide Vietnamese learners with portable, verifiable credentials through two initiatives: a personalized learning mobile app for high school and university students, and a learning management platform for schools. The initiatives integrate Open Campus ID and its verifiable credentials with the aim to modernize school operations nationwide.
Digi Yatra plans expansion to international travel with passport-based enrolment
Speaking with L.V. Navaneeth, CEO, The Hindu Group, Digi Yatra Foundation CEO Suresh Khadakbhavi addressed concerns around data security, stating Digi Yatra follows a decentralised architecture in which credentials reside on users’ own devices rather than in a central database
Indicio enables AI agents to verify Digital Travel Credentials
Once the traveler presents the credential to the agent, the AI travel agent cryptographically verifies that the information in the credential is authentic. After the verification is complete, the agent can help book rental cars and airlines, find the fastest route to a destination, book a hotel or an excursion, and change reservations, the firm explains in a blog post.
NIST develops playbook for online use cases of digital credentials in financial services:
Panel on mDLs explores efforts by NIST, AAMVA to show benefits of digital credentials. NIST’s work on mDLs gets an airing at the FIDO Identity, Authentication, and the Road Ahead 2026 conference, in a panel focused on how NIST’s partnerships have advanced the digital ID sector. Panelists include Jeremy Grant, coordinator of the Better Identity Coalition; Ben Amsterdam of PNC Bank; Tim Maru, portfolio director for identity credentialing the American Association of Motor Vehicle Administrators (AAMVA); and Ryan Galluzzo, who leads NIST’s digital identity program.
Utah Advances Policy-First Digital Identity Framework Centered On Individual Control
The state moves to authorize a digital identity framework emphasizing open standards, privacy and durable public policy nationwide.
UNICEF in search of firm to co-design youth digital credentialing system
Companies or organizations with expertise in digital identity, credentialing, and education technology, have up to February 16 to bid for the contract.
Morocco Signs Cooperation Agreements with iDakto and ShareID for National Digital Wallet
Morocco’s Ministry of Digital Transition and Administrative Reform has signed cooperation agreements with French firms iDakto and ShareID to support development of a national digital identity wallet, the ministry announced February 12. The project sits within Morocco’s broader Idarati X.0 public-sector digital modernization program and is designed to provide secure digital identity infrastructure for accessing public services and conducting online transactions.
Singapore and India engage in cross-border DPI through verifiable employment credentials
IMDA’s pilot converts background checks into cryptographically signed credentials stored in the individual candidate’s digital wallet, making employment verification much faster, easier and safer for Singapore businesses.
The “Agent” Dilemma: How Blockchain Could Save Patient Privacy in a $500B AI Market
However, while AI’s promise of unprecedented efficiency and innovation is alluring, such rapid proliferation raises a number of serious concerns, namely around protecting patients’ privacy and sensitive health data. How can a system that comprises countless semi-autonomous AI systems with potentially unclear directives guarantee that people’s personal information won’t be misused – even by accident?
One promising approach is self-sovereign identity (SSI) – a blockchain-based solution that empowers patients to control their data with precision and security.
Control Without Ownership in the Era of Self-Sovereign Identity:
The situation calls for change. The concept of “control without ownership” outlined by Gorgiladze offers a viable legal framework that aligns technological capabilities of self-sovereign identity with existing legal systems. It provides a practical direction for the evolution of digital identity regulation—one that balances innovation, autonomy, and legal certainty.
Decentralized Identity (DID) for B2C: Consumer Self-Sovereign Identity
This article covers the shift from centralized data silos to consumer-owned identity models and how did tech reduces breach surface areas for modern apps. You’ll learn about verifiable credentials and why moving away from passwords is the only way to truly protect user privacy while keeping iam flows simple for devs.
Bringing Identity Back to the Human: What Self-Sovereign, Human-Centered Identity Looks Like in Practice (2026)
For decades we outsourced our digital selves. Governments issued numbers, platforms built profiles, companies stored credentials, and we handed over the keys to our identity in exchange for convenience. But externalizing identity handed control to systems never designed to carry the weight of a human life. Those systems optimized for extraction, scale, and monetization—not dignity, privacy, or truth. Now the question is no longer theoretical: What does it look like to bring identity back to the human?
[Research] QR-MetaSSI: A Quantum-Resistant Self-Sovereign Identity Framework for Metaverse Platforms
This paper proposes QR-MetaSSI, a framework integrating NIST-standardized post-quantum cryptography with W3C-compliant Self-Sovereign Identity principles to secure metaverse platforms against quantum threats, demonstrating through simulation that lattice-based DIDs and hash-based verifiable credentials can maintain authentication latency under 150ms with 128-bit quantum security at reasonable computational overhead compared to classical ECC-based systems.
(Heather Flanagan) Contributor Skills: How Standards Are Created
(Indicio) [slide deck] Decentralized Identity in 2026: The Opportunities for Business
DIF Welcomes Kyndryl as Associate Member to Advance Secure, Decentralized AI Ecosystems
Advancing Trust in Agentic AI: Kyndryl’s Agentic AI Framework envisions a future where autonomous AI agents interact seamlessly across open, cross-domain ecosystems. Through DIF’s Trusted AI Agent Working Group, Kyndryl will contribute to defining standards that enable agents to establish strong trust. The Working Group addresses authentication, authorization, and delegation, allowing industry players to collaborate safely and reliably.
(Evercred) How U.S. Agencies Can Prevent Fake Credentials Using Digital Credential Verification in 2026
The rise of deepfake technology allows bad actors to create realistic but fraudulent certificates. These documents often pass visual inspections. Agencies need a system that relies on cryptographic proof rather than visual markers.
By 2026, the cost of employment-related fraud has grown significantly. Government IT departments must prioritize systems that detect fake credentials before an individual enters the secure network.
[Research] Trustworthy Blockchain-based Federated Learning for Electronic Health Records: Securing Participant Identity with Decentralized Identifiers and Verifiable Credentials
This paper proposes a blockchain-based federated learning framework that uses Self-Sovereign Identity standards (DIDs and Verifiable Credentials) to enable secure, privacy-preserving AI model training across healthcare institutions, successfully preventing Sybil attacks while maintaining strong clinical performance.