Identosphere 166 March 1-15: Agentic AI and Identity lots of articles • Monetizing DPI • new DCC report • LFDT Progress Report
This is the mostly weekly Identosphere Newsletter sharing highlights from around the web covering Decentralized and Self-Sovereign Identity curated by Kaliya Young, Identity Woman.
New Upcoming
OAuth Security Workshop (OSW) 2026, Leipzig, Germany, from May 27–29, 2026.
The OAuth Security Workshop is the premier forum for in-depth technical discussions on OAuth, OpenID, and related technologies. By fostering direct and open collaboration between industry professionals, academic researchers, and members of standardization groups, OSW has uniquely helped shape and improve internet protocols.
Leading researchers also attend to showcase cutting-edge results on identity protocol security. OSW serves as an essential independent venue for cross-pollination between the OpenID Foundation, IETF OAuth, and GNAP working groups.
Upcoming
KERICONF26 April 21-23 2026, Lehi, Utah (US)
OIDF Workshop April 27th, San Jose
Internet Identity Workshop #42, April 28-30, 2026, Mountain View California (Sponsorships Available)
Agentic Internet Workshop #2, May 1, 2026, Mountain View California (Sponsorships Available)
dice: Digital Identity unConfernece Europe (an IIW Regional Event) June 22-24, Copenhagen, Denmark (Sponsorships Available)
Opportunities
Competitive DPI Deployment
The Centre for Digital Public Infrastructure - CDPI is inviting System Integrators, GovTechs, and Digital Service Providers to express interest in upcoming competitive opportunities to deploy DPI as scalable, packaged solutions (DaaS).
Trust
Decentralized Trust Infrastructure at LF: A Progress Report
👑 If everybody and their dog has a definition of 𝐝𝐢𝐠𝐢𝐭𝐚𝐥 𝐬𝐨𝐯𝐞𝐫𝐞𝐢𝐠𝐧𝐭𝐲,
I suppose I’m allowed to give it a stab, too 😬
𝒀𝒐𝒖 𝒂𝒓𝒆 𝒔𝒐𝒗𝒆𝒓𝒆𝒊𝒈𝒏 𝒐𝒗𝒆𝒓 𝒔𝒐𝒎𝒆𝒕𝒉𝒊𝒏𝒈 – 𝒂𝒔 𝒂𝒏 𝒊𝒏𝒅𝒊𝒗𝒊𝒅𝒖𝒂𝒍 𝒐𝒓 𝒂𝒔 𝒂𝒏 𝒐𝒓𝒈𝒂𝒏𝒊𝒔𝒂𝒕𝒊𝒐𝒏 - 𝒊𝒇 𝒚𝒐𝒖𝒓 𝒓𝒊𝒈𝒉𝒕𝒔 𝒐𝒗𝒆𝒓 𝒕𝒉𝒂𝒕 𝒕𝒉𝒊𝒏𝒈 𝒂𝒓𝒆 𝒑𝒓𝒐𝒕𝒆𝒄𝒕𝒆𝒅 𝒂𝒏𝒅 𝒚𝒐𝒖 𝒂𝒓𝒆 𝒆𝒏𝒂𝒃𝒍𝒆𝒅 𝒕𝒐 𝒆𝒙𝒆𝒓𝒄𝒊𝒔𝒆 𝒕𝒉𝒆𝒎 (𝘮𝘦𝘢𝘯𝘪𝘯𝘨: 𝘵𝘩𝘦 𝘭𝘦𝘨𝘢𝘭 𝘴𝘺𝘴𝘵𝘦𝘮 𝘸𝘪𝘭𝘭 𝘢𝘤𝘵𝘶𝘢𝘭𝘭𝘺 𝘥𝘰 𝘴𝘰𝘮𝘦𝘵𝘩𝘪𝘯𝘨 𝘸𝘩𝘦𝘯 𝘺𝘰𝘶𝘳 𝘳𝘪𝘨𝘩𝘵𝘴 𝘢𝘳𝘦 𝘯𝘰𝘵 𝘳𝘦𝘴𝘱𝘦𝘤𝘵𝘦𝘥).
Why digital estates need standards, and why we need them now
Today, the OpenID Foundation released The Unfinished Digital Estate - the first comprehensive framework addressing this universal challenge. Developed by the foundation’s Death and the Digital Estate (DADE) Community Group, the report doesn’t just document the problem. It calls for coordinated action across governments, technology platforms, and industries to build the infrastructure we need.
(Politico Opinion) [Frank McCourt] Personal data is the new battleground for democracy
To reverse that reality, we must build alternative systems that respect individual rights, return ownership and control of personal data to individuals, and align with democratic principles. The technologies shaping our lives need to be optimized to protect citizens, not endanger them.
Education
Proof of Knowledge
POK implements portable digital credentials, aligned with Open Badges 3.0 and the European Learning Model as non-fungible tokens (NFTs) on the blockchain. In the Community Call, Tomás will address a number of topics at the intersection of education and technology — including AI and digital learning — and explain how digital credentials allow us to take advantage of these tools in service of equity, opportunity, and trust.
(Digital Credentials Consortium) [Report] The Essential Guide to Interoperability: From Paper Trails to Opportunity Pathways
However, too often credentials are locked inside proprietary platforms, rejected by Applicant Tracking System (ATS) filters that cannot parse the data, or not trusted because they cannot be quickly verified. (link to report)
Identity and AI
Agent Identities: everything you need to know
For over two decades, my work has kept circling back to one hard problem: how do machines prove they can be trusted?
Agents have raised the stakes: they take autonomous actions. Without cryptographic identity, we can’t authenticate requests, authorize actions, or attribute decisions.
Agents Are More Like Humans Than Workloads. Here’s Why That Matters for Identity.
Agents are the consultant, not the robot arm. Workload identity is built for maps: you know the territory, you draw the routes, if a service goes off-route it’s an error. Agent identity is built for compasses: you know the destination, but the route is discovered at runtime. Our identity infrastructure needs to reflect that difference.
Over the past year I have been reading a growing body of papers on digital public infrastructure, AI governance, agent systems, and digital identity. Many of these works raise important questions, but the insights are scattered across journals, policy blogs, research archives, and essays. It becomes difficult to track how the ideas connect, where the assumptions differ, and which architectural claims actually hold up under scrutiny.
ResilientCyber LinkedIn post: AI Agent Authentication and Authorization
The core model treats agents as workloads with a full identity stack, identifiers, credentials, attestation, provisioning, auth, observability, and compliance.
IETF Internet Draft: AI Agent Authentication and Authorization (draft-klrc-aiagent-auth-00)
This document proposes a model for authentication and authorization of AI agent interactions. It leverages existing standards such as the Workload Identity in Multi-System Environments (WIMSE) architecture and OAuth 2.0 family of specifications. Rather than defining new protocols, this document describes how existing and widely deployed standards can be applied or extended to establish agent authentication and authorization. By doing so, it aims to provide a framework within which to use existing standards, identify gaps and guide future standardization efforts for agent authentication and authorization.
Organizing the Landscape of DPI, AI, Governance, Agent Systems and Digital Identity
Over the past year I have been reading a growing body of papers on digital public infrastructure, AI governance, agent systems, and digital identity. Many of these works raise important questions, but the insights are scattered across journals, policy blogs, research archives, and essays. It becomes difficult to track how the ideas connect, where the assumptions differ, and which architectural claims actually hold up under scrutiny.
Ryan S. Adams: Nate Liason Built a Zero-Human Company Run by an AI CEO
Nate Liason built a company generating $80K in 30 days (~$1–2M ARR) run entirely by an AI CEO named Felix, built on Claude, with a total startup cost of $1,500 and $400/month in ongoing expenses.
Phil Windley: Cross-Domain Delegation in a Society of Agents
Windley argues that cross-domain delegation between AI agents — where the delegating system no longer controls the enforcement point — only works reliably within a “society of agents” that combines three mechanisms: policies that deterministically constrain behavior within each domain, promises (signed structured commitments derived from an agent’s own policy set) that communicate intent across domains, and reputation as decentralized social memory that tracks whether those promises are honored over time.
LF Decentralized Trust: Decentralized Trust Infrastructure at LF — A Progress Report
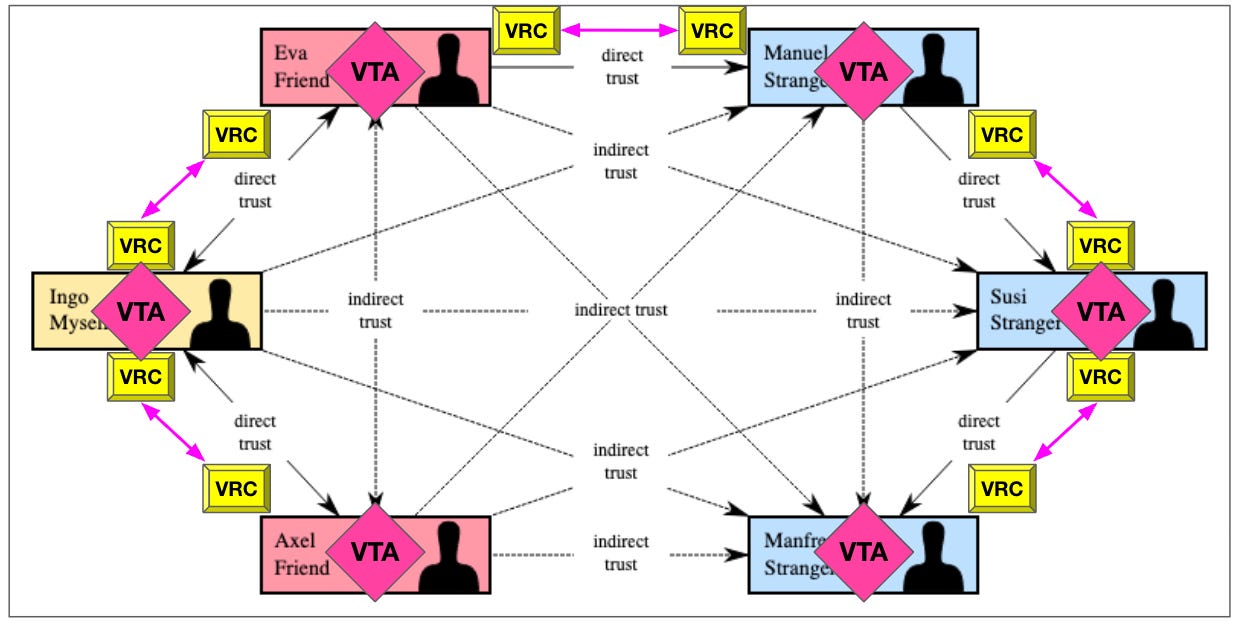
Written by Drummond Reed in response to a challenge from Linux Foundation CEO Jim Zemlin following the XZ backdoor attack, this post describes how the Trust Over IP Foundation is building a Decentralized Trust Graph (DTG) model — using DIDs, Verifiable Relationship Credentials, zero-knowledge proof-based Personhood Credentials, and Verifiable Trust Agents — to replace the fragile PGP web-of-trust model for verifying open source contributors at scale. At the 2026 LF Member Summit, Affinidi contributed three new LFDT Labs including OpenVTC, a deployable “VTC in a box” for open source projects, with a goal of having the Linux kernel project test it at the Linux Kernel Maintainer Summit in Prague in October 2026.
When AI Starts Buying for You, Trust Becomes the Product
Mastercard’s Chief Digital Officer Pablo Fourez announces Verifiable Intent, a new open, standards-based trust layer for agentic commerce co-developed with Google, which creates a tamper-resistant, privacy-preserving cryptographic record linking a consumer’s identity, intent, and authorized actions when an AI agent transacts on their behalf. Built on specifications from FIDO Alliance, EMVCo, IETF, and W3C, the specification and an initial reference implementation have been open-sourced on GitHub, with integration into Mastercard Agent Pay’s intent APIs planned for the coming months.
Anthropic and the Pentagon
Schneier and Sanders argue that while Anthropic’s stand against Pentagon demands for mass surveillance and autonomous weapons AI looks principled, it’s largely strategic posturing — and the real solution isn’t corporate heroism but stronger democratic laws governing military AI.
You Don’t Give Agents Credentials. You Grant Them Power of Attorney.
Agents don’t need your identity. They need your authority.Those are not the same thing. Identity establishes who the agent is. Authority governs why it is acting, under what conditions, and when it must stop. We have been granting the first and assuming the second follows. It does not.
Puritan Economics Can Teach Us About Agentic AI in a Capitalist Economy
TwinAI Inc - what are its implications and how do we give them credentials
It’s why we set up Trusted Agents.
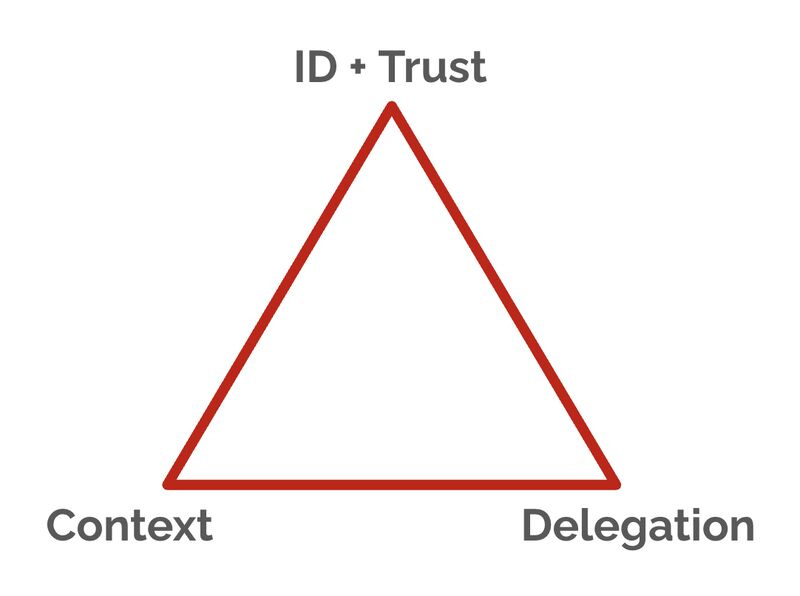
The picture below is our ‘Agentic Commerce Triangle’ framework, which we use with clients for strategic planning. Because we don’t just need delegation to AI Agents. We also need ID and trust, and portable customer context.
More coming on the triangle soon.
If you need help making sense of AI Agents, or want to build your market response for agentic commerce, get in touch.
(Phil Windley) Cross-Domain Delegation in a Society of Agents
Cross-domain delegation requires more than transferring a credential. In a society of agents, policies define boundaries, promises communicate intent derived from those policies, credentials carry delegated authority, and reputation allows trust to emerge through repeated interactions.
(Phil Windley) Delegation as Data: Applying Cedar Policies to OpenClaw Subagents
Intra-domain delegation enables an agent to grant constrained authority to subagents without expanding the system’s trust boundary. In the OpenClaw + Cedar demo, delegation is modeled as data and enforced by a stable policy set, preserving policy integrity while allowing dynamic scoping of power.
OAuth SPIFFE Client Authentication
Government News
[UK] Government wants to build digital ID system in-house
The Home Affairs Committee hearing on digital ID reveals consultation is due next week; there will be no central database; and while government wants to build the system in-house, it will not replace private digital ID providers
Monetizing Digital Public Infrastructure
Aadhaar provided high-quality data, actionable intelligence, and a trusted nation-scale process for verifying identity. Going from identity to impact will require an actionable framework that can baseline SDG status, provide transparency into underserved communities and geographies, identify gaps, make targeted investments, and quantify the return on investments. It will require reforming service delivery models, adopting best practices, and continuous and consistent monitoring of progress toward the goals.
[Response] (INATBA) Privacy is not a secondary feature. It’s the foundation of the EUDI Wallet.
Interesting Enterprise Developments in Identity
The Future of Identity: Self-Service Account Recovery (Preview) in Microsoft Entra
The transition to a passwordless world is incomplete if the “back door” (recovery) remains open and insecure. By integrating government-grade identity verification directly into the login flow, Microsoft Entra provides the final piece of the puzzle: a recovery method that is as secure as the primary login itself.
Virtual Coffee Chat Recap – March 2026
The Trusted Credential Adoption Group: Six Use Cases to Watch
The Trusted Credential Adoption Group (TCA Group) shared an update on its progress across six priority use cases for credential adoption in Aotearoa, including bank account opening, KYC (Know Your Customer), and lost phone / device recovery verification. The group is targeting a May deadline for market communications. Anyone interested in contributing or observing is welcome – reach out to the DINZ team to find out more.
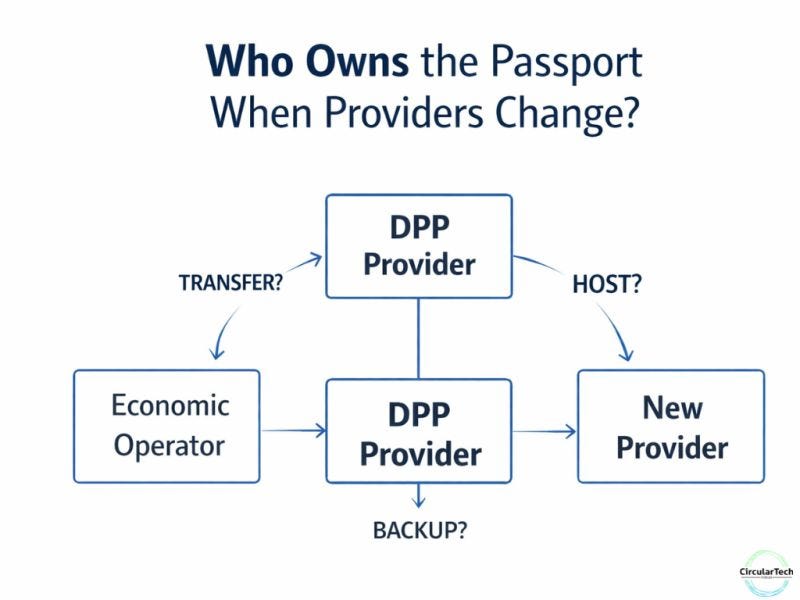
If we don’t solve Digital Product Passport portability now….
(Kantara Initiative) Publication Notice: SP 800-63A-4 Service Assessment Criteria (SAC)
Kantara Initiative announces the formal publication of the Kantara Identity Assurance Framework: SP 800-63A-4 Service Assessment Criteria (SAC) & Statement of Criteria Applicability (SoCA), aligned to NIST Special Publication 800-63A Revision 4 – Identity Proofing.