Identosphere 167 March 14–28, 2026: MCP-I Comes to DIF • Digital Sovereignty Needs More Than Code • Identity Protocols Meet AI Agents
This is the mostly weekly Identosphere Newsletter sharing highlights from around the web covering Decentralized and Self-Sovereign Identity curated by Kaliya Young, Identity Woman.
New Upcoming
Neocypherpunk Summit #2 — June 14, Berlin — Web3Privacy Now. Cypherpunk activism and culture event at Funkhaus Berlin, building on a 2025 event that drew 10,000 attendees.
Upcoming
KERICONF26 April 21-23 2026, Lehi, Utah (US)
OIDF Workshop April 27th, San Jose
Internet Identity Workshop #42, April 28-30, 2026, Mountain View California (Sponsorships Available)
Agentic Internet Workshop #2, May 1, 2026, Mountain View California (Sponsorships Available)
OAuth Security Workshop (OSW) 2026, Leipzig, Germany, from May 27–29, 2026. The OAuth Security Workshop is the premier forum for in-depth technical discussions on OAuth, OpenID, and related technologies.
dice: Digital Identity unConfernece Europe (an IIW Regional Event) June 22-24, Copenhagen, Denmark (Sponsorships Available)
Infrastructure Under the Sea
European Commission Conference — Submarine Cable Security — Hugh Gardner
Actually about subsea cable infrastructure security and strategic risk management, not identity.
Standards News
URN:SAID Namespace Registered by IANA — LF Decentralized Trust
IANA formally registered the “urn:said” namespace, enabling Self-Addressing Identifiers from the KERI ecosystem to integrate with broader internet standards.
MCP-I (Model Context Protocol for Identity) Comes to DIF — Kim Hamilton Duffy → Blog post
The Decentralized Identity Foundation now hosts MCP-I, bringing decentralized identity standards into the Model Context Protocol ecosystem.
Dock Labs MCP Server for AI Credential Management — Jeff Stephens → Article
Dock Labs released an MCP server enabling AI agents to issue and verify credentials while enforcing least-privilege access controls.
World’s AgentKit: Iris Scan Identity Tokens for AI Agents — Elaine Groh → Ars Technica
World’s AgentKit uses iris-scanning and cryptographic identity tokens to prevent AI agent swarms from launching Sybil attacks on online services.
Enterprise & Supply Chain
Digital Handover for Cotton Supply Chain — Joris van Vliet / Fibre Forward
A multidisciplinary team is building a digital handover mechanism for cotton supply chain transparency using digital product passports.
AI Agents & Identity
The foundational model companies aren't going to solve AI agent identity alone. — Cole Grolmus
The AI agent identity market is fragmented, and whoever controls the narrative first will likely win — foundational model companies won’t solve this alone.
The Proof Gap
Verification systems were built for a world where humans did the verifying. Agents are arriving to find the door still locked.Human judgment can’t scale to the volume or speed of machine-generated content — cryptographic verification is the necessary next step for the agentic economy.
No Organisation is Ready for AI-Empowered Customers — David Birch
Customers armed with AI agents will demand transparency and make purchasing decisions faster and more ruthlessly than humans ever could — and no organization is prepared.
When Browsers Start Acting for You — AI Browsers and Identity — Heather Flanagan
If AI-powered browsers act autonomously on behalf of users, do they still meet the W3C’s definition of a “Web User Agent”?
Privacy-Preserving Tech Landscape / SSI as Trust Layer for AI — Kamlesh Nagware
Self-Sovereign Identity ecosystems with DIDs and verifiable credentials are becoming essential trust infrastructure for autonomous AI systems.
Trusted AI, Safe AI, Blockchain — Kamlesh Nagware
Three pillars for trustworthy AI: guardrails (what can be enforced outside the model), alignment (does the model follow the right path), and governance through regulation.
European & UK Digital Identity
Britons to be paid £550 to judge controversial digital ID scheme — Stuart Young
The UK government is paying 120 citizens £550 each to participate in a consumer panel evaluating the national digital ID scheme, costing roughly £830,000 total.
UK Government Adopting Verifiable Credentials for Digital ID — Jamie Smith
After eight years of advocacy, the UK government has announced plans to implement verifiable credentials for digital ID — a milestone for the community.
eIDAS2 / EU Digital Identity Wallet
Worldline announces the shift to Europe’s Digital Identity Wallet is underway, highlighting regulatory milestones and interoperability across 27+ wallets.
EUDI Wallet Adoption — Chicken-and-Egg Problem — Nick Lambert
The EU is mandating business integration by late 2027 to jumpstart citizen usage and overcome the EUDI Wallet’s chicken-and-egg adoption challenge. Will the EUDI become something people actually rely on in their daily lives… or just another piece of infrastructure that exists on paper?
PwC Map of Digital Identity Adoption — Tobias Bojesen
PwC published a map examining digital identity adoption across 42 countries, emphasizing that the real challenge is cross-border interoperability through eIDAS2.
Standards & Interoperability
How to Measure Digital Transformation Success with Verifiable Credentials — SpruceID
Digital transformation success should be measured through resident outcomes and operational efficiency, not just credentials issued or system launch dates.
IDEMIA/Indicio White Paper: Decentralized Identity for Financial Services — Indicio
Verifiable digital credentials combined with authenticated biometrics establish a cryptographically-secure identity framework for financial services fraud, compliance, and efficiency.
The physical card has been dying since 2014.
The card keeps evolving. New materials, new form factors, new experiences. It's only dead for those who stopped paying attention
DIF Welcomes Aven Hospitality as Associate Member — Decentralized Identity Foundation
DIF welcomed Aven Hospitality to collaborate on trusted, interoperable identity standards for the travel and hospitality industry.
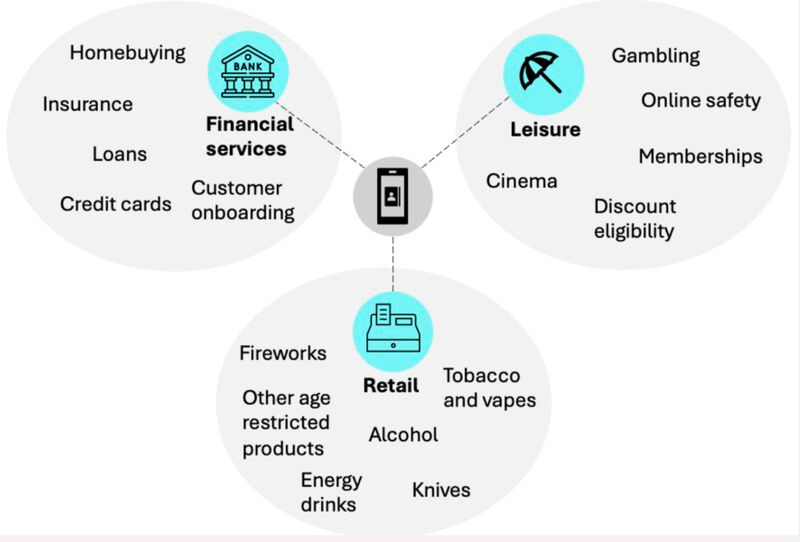
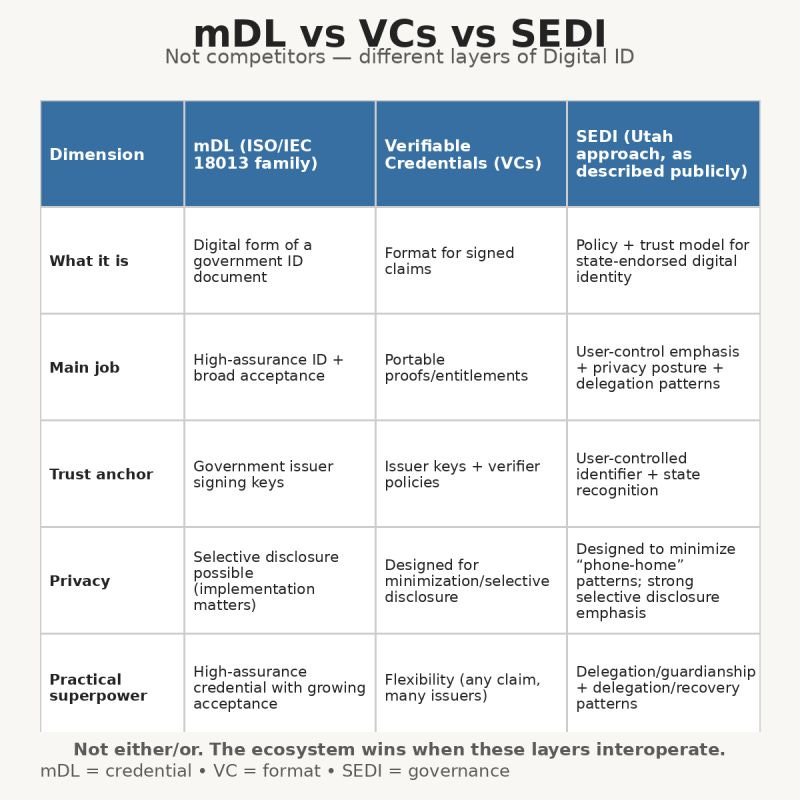
mDL vs VC vs SEDI — Jiten Valecha
SEDI, mDL, and Verifiable Credentials are complementary layers of digital identity infrastructure rather than competing technologies, each serving distinct functions.
Biometrics & Fraud
Biometrics Sounds Cool—and Safe. Maybe, but Read This First — WSJ w/ Pushback from Maxine Most
Maxine Most pushes back on a Wall Street Journal article about biometrics, arguing the industry needs better public education on how the technology actually works.
46 Bank Accounts Opened with Deepfakes at ABN AMRO — Parya Lotfi
A fraudster opened 46 bank accounts at ABN AMRO using deepfake-manipulated identity documents, exposing critical vulnerabilities in current KYC and biometric verification.
Sora Shutdown & Deepfake Normalization — Sam Gregory (WITNESS)
OpenAI shut down Sora, but the cultural normalization of hyper-realistic synthetic video during its six-month run will persist long after the platform disappears.
Thoughtful
Technology Paternalism — A Case for Self-Sovereign Identity — Martina → LinkedIn
Technical systems shape user choices through design, algorithms, and infrastructure — “Technology Paternalism” — with deep implications for digital identity and autonomous AI.
Decentralization, Identity & Future of AI — Slava Tykhonov
DIDs and digital identity infrastructure could become foundational for AI systems, enabling ownership and control of data in a new economy built on verifiable credentials.
Who holds the keys to digital sovereignty? It might not be who you think — Biometric Update
Cryptographic key control matters more for digital sovereignty than physical data storage location.
Blockchains That Cancelled Each Other Out — Timo Hotti
Combining identity and transaction models in blockchain architecture eliminates the need for blockchain altogether — the industry spent years optimizing a flawed foundation.
“Identity is the most misunderstood layer in financial services.” — Panagiotis Kriaris
Identity verification has evolved from manual to digital to verified systems, but fragmentation across 150+ government schemes demands a unified orchestration layer.
22 Years in Identity and Access — Tim Nicholls
The IAM industry keeps rebranding existing solutions with new acronyms rather than delivering genuine innovation — it confuses rather than helps customers.
Digital Sovereignty & Open File Formats — Kai Hartung
Digital sovereignty and open-source technology are essential for maintaining independence from centralized platforms.
Digital Sovereignty Needs More Than Cold Code it needs Trust by Design — Nugraha Dewanto
Digital sovereignty in the Global South fails not at the infrastructure level but earlier, when state institutions lack the trust needed to make technical systems legitimate.
Alternative Pathways: Blockchain for Identity of Stateless Persons — Dr. Maria-Gabriela Sarmiento
Decentralized technology could help restore legal identity for over one billion stateless individuals, refugees, and undocumented migrants worldwide.
Government & AI Policy
Center Aisle Portal — Making Sense of AI Policy
Brown University’s Center for Technological Responsibility launched a portal to help the public navigate the 1,000+ AI-related bills introduced across the U.S.
World Privacy Forum’s Third Annual WACV Privacy Tutorial: Machine Unlearning, AI Governance, and Privacy — Pam Dixon
Machine unlearning is emerging as a requirement in AI governance and privacy law, addressing how models can be made to “forget” personal data.