Identosphere 241 Aug 18-24: More AI Agent Identity • Apple ID Annoucements • Login.gov + Passports • OID4VC Security Review•
A weekly review of News and Updates for and from the Decentralized and Self-Sovereign Identity Community.
Thank you to all of you who filled out the poll. It is still live. It should only take about 5 min.
UpComing
Proving Identity in Provenance, by Content Authenticity Initiative, August 27, 12-12:45
Center for Digital Public Infrastructure presents Credentials in Action: Public Innovation Challenge Registration closes 1 September 2025.
Internet Identity Workshop Mountain View, October 21-23, 2025
Notice of Vote to Approve OpenID for Verifiable Credential Issuance 1.0 Final Specification
The two-week voting period will be between Monday, September 1, 2025 and Monday, September 15, 2025, once the 60 day review of the specification has been completed.
Qualified Verifiable Data Registries (qVDR) as the Foundational Component of Digital Public Infrastructure (DPI)
We explain DPI in practical terms for policymakers, drawing parallels to energy infrastructure and citing real-world DPI implementations (e.g. India’s Aadhaar, UPI, DEPA and Europe’s emerging initiatives like the European Business Wallet, Manufacturing-X, Catena-X). We then clarify the concept of Verifiable Data Registries (VDRs) and the added value of “qualification” — i.e. meeting rigorous standards (as seen in eIDAS 2.0’s Qualified Electronic Ledgers) to ensure trustworthiness.
OIDF receives security analysis of OpenID for Verifiable Presentations
These proofs confirm the security of the protocol within the bounds of the mathematical assumptions and formal modelling. Importantly, no new vulnerabilities were identified during the verification process.
The complete report is available here on the DCP WG homepage for review by implementers and the broader community.
iOS 26 Brings Digital IDs to Apple Wallet: Will This Push Adoption?
1. Digital Passport in Wallet
2. “Verify with Wallet” for Web and App Logins
3. Standards-Based Architecture: W3C Verifiable Credentials & FIDO
AI Agents & Identity
Report: IA Agent Governance a Field Guide
The report shows that agentic AI still struggles with complex, real-world tasks. Benchmarks reveal large performance gaps, with agents scoring far below humans on everyday tasks (GAIA 15% vs. 92%), complex coding (SWE-bench drops from 20% to 0%), research tasks (RE-Bench only ahead in 2-hour tasks), and web navigation (WebArena 14% vs. 78%).
Research: IDs for AI Systems
This research proposes creating identification systems (IDs) for AI instances to address the current lack of transparency around AI system safety, accountability, and control - such as not knowing who to contact when systems malfunction or being unable to verify safety certifications. The proposed ID framework would assign unique identifiers to specific AI system instances (like individual chat sessions) and make relevant information accessible to users, investigators, and other stakeholders, particularly for high-impact applications like financial transactions or human interactions.
Understanding the Impacts of Generative AI Use on Children
This research highlights a critical gap in generative AI research: while there's extensive study of the technology's potential impacts and risks, there's insufficient focus on how it affects children, despite AI already being integrated into games, educational platforms, and other child-facing products. The authors argue that children, who may be the most impacted by widespread AI deployment, are paradoxically the least represented in AI design, development, and governance decisions, despite having particular needs and rights that require special consideration.
The Role of Decentralized Identity in Agentic Security
From Identity to Enforcement: DIDs + VCs
You can’t enforce principalhood with session cookies or baked-in API keys. You need identities that are verifiable and portable. Decentralized Identifiers (DIDs) provide tamper-resistant, resolvable identifiers for agents, users, publishers, and services.
By implementing Verifiable Credentials (VCs), claims can be attached to those DIDs: roles, regional limits, velocity caps, expiry, whatever the policy needs, and those claims can be checked on every request. In short: identity + credential becomes policy-enforceable capability.
(SC Media) AI agents need both tougher standards and stricter identity controls
"The industry needs a new way to fully manage the AI agent lifecycle: an identity-security standard that gives enterprises confidence in what agents can access and gives developers freedom to build experiences that are secure and seamless by default," said Todd McKinnon, CEO and Co-Founder of Okta, in his introduction to the webinar.
What are Politically Exposed Persons Anyways?
(uqudo) Ensuring Compliance: Optimizing PEP Screening Processes
Politically Exposed Persons encompass a broad universe of individuals whose positions create inherent vulnerabilities to corruption.
Research
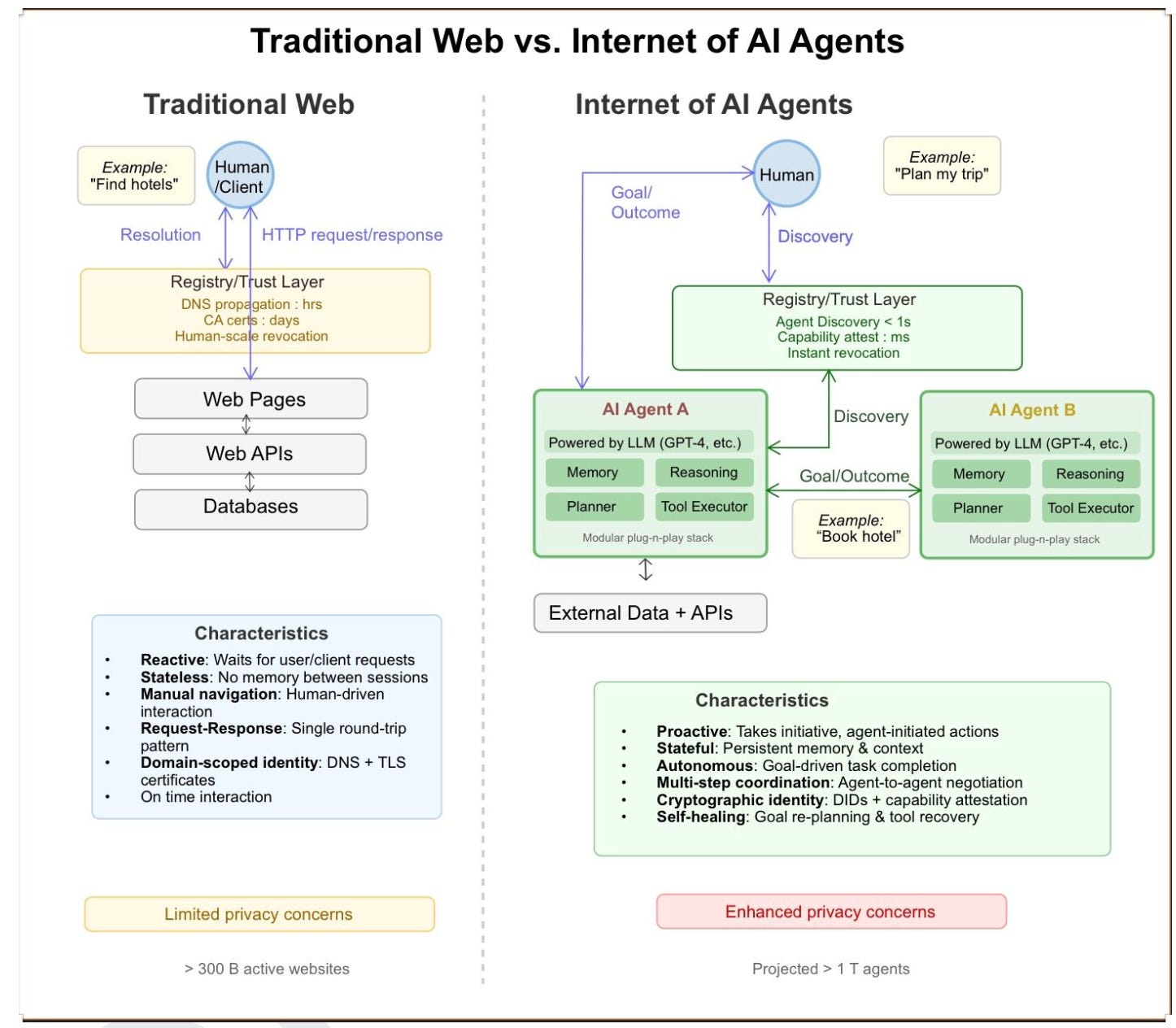
Upgrade or Switch: Do We Need a New Registry Architecture for the Internet of AI Agents?
Privacy-Preserving Credentials in Decentralized Identity: Integrating Zero-Knowledge Proofs from Theory to Practice
This research systematically analyzes four major zero-knowledge proof protocols (Groth16, PLONK, Halo2, and Bulletproofs) to determine their compatibility with decentralized identity systems that prioritize user control and privacy. The authors design a privacy-preserving credential architecture and provide practical guidelines for deploying these cryptographic solutions in real-world decentralized identity environments, marking the first comprehensive study to bridge the gap between ZKP theory and practical DID implementation.
A DID-based one-time session key authentication mechanism for secure human-AI chatbot communication
This paper addresses security vulnerabilities in AI chatbot-based Robotic Process Automation (RPA) systems, which are increasingly used for sensitive tasks like email management and complex workflows but face risks from traditional PKI-based authentication that stores personal information within the system. The authors propose a new authentication mechanism using Decentralized Identity (DID) technology with one-time session keys, which provides better privacy protection, session independence, and demonstrates superior time efficiency compared to PKI-based systems when performing multiple authentications, while maintaining very low probability of security threats.
VCs showing up in Interesting Places
GSA’s Login.gov launches passport-based identity verification
As a new option for users to securely verify their identity online, Login.gov users will be able to capture a picture of their U.S. passport biographical data page during the remote identity proofing flow. Login.gov will then check against U.S. passport records via a privacy-preserving application programming interface (API) operated by the U.S. Department of State.
AfriProof: Own Your Genius
VCs meet NFT
AfriProof is a decentralized intellectual property (IP) protection and enforcement platform built on Hedera Hashgraph, designed to empower African creators artists, musicians, inventors, writers, and designers to securely register, verify ownership, and legally defend their creative works.
[Polkadot] (Forum Post) Proposal: Leveraging Proof of Personhood & Verifiable Credentials to Protect the OpenGov Treasury
I’m proposing we explore integrating Verifiable Credentials (VCs) as a layer for treasury funding, using PoP as a fundamental pillar.
US Treasury’s DeFi ID plan is ‘like putting cameras in every living room’
Last week, the agency opened a consultation under the Guiding and Establishing National Innovation for US Stablecoins Act (GENIUS Act), which was signed into law in July. The Act directs the Treasury to evaluate new compliance tools to fight illicit finance in crypto markets.
One idea was embedding identity credentials directly into smart contracts. In practice, this would mean a DeFi protocol could automatically verify a user’s government ID, biometric credential, or digital wallet certificate before allowing a transaction to proceed.
Balcony Has Big Plans for Public-Sector Blockchain
Earlier this year, Bergen County, N.J., part of the New York City metro area, hired Balcony to use blockchain — a decentralized digital ledger often described as a “spreadsheet in the sky” — for property records management.
Bridging Privacy and Public Blockchains: Reflections from the Privacy for Financial Services Workshop
At the inaugural Privacy for Financial Services Workshop hosted by LF Decentralized Trust in New York, a clear signal emerged: privacy is no longer a theoretical aspiration in digital finance. It’s a necessity, and it’s becoming deeply practical.
Y Combinator's Youngest Solo Founder Says Digital Identity Is The Internet's Biggest Infrastructure
Kirill: As AI platforms integrate deeper into the internet, politicians will see the only way to ensure "safety" is by introducing identity requirements. But they have no clue how the technology works and will choose the easiest route - what the UK and EU are doing now.
Centralized and Decentralized Systems: A Symbiosis for Greater Prosperity – Insights from Organization Theory
In short, decentralized and centralized systems can form a beneficial symbiosis that compensates for the drawbacks of monolithic approaches and generates more prosperity for all participants. Hybrid models, as recommended in organization theory, combine stability with agility and are exceptionally sensitive in complex environments.
(Heather Flanagan) Working Group Chair Skills: Standards Work Isn’t Just for Coders
A good chair brings the right working group chair skills to the table:
- Manages time, the agenda, and the meeting queue.
- Keeps the room neutral and separates their “chair hat” from their personal opinions.
- Tests for consensus and documents objections.
- Guides the group back to its charter when things start to sprawl.
Thoughtful Beyond Identity
Sovereignty and Landscape: On digital sovereignty — Part I
The author argues that digital sovereignty discussions are inadequate without proper landscape mapping, demonstrating through a 2015 automotive case study how Wardley Maps can identify where sovereign borders should be drawn by analyzing user needs, component evolution, and value embedding rather than just focusing on data or supply chains.
Societal versus Market benefit: On digital sovereignty — Part II
The author demonstrates through mapping exercises across multiple industries including healthcare that societal investment priorities have only a 3% overlap with market priorities, arguing that governments must consciously choose between serving market interests versus societal needs when making sovereignty-related investment decisions, as the two are fundamentally different despite market claims to serve society.
Whose interests are you serving? On digital sovereignty — Part III
The author argues that AI systems act like "Wormtongue" by embedding specific cultural values and biases (particularly market-focused, US-centric ones) into societies that use them for policy-making and education, warning that governments must understand what values these systems were trained on before allowing them to influence their cultural systems and decision-making processes.