Identosphere #28 • DID:UN-DID • Interop Mapping • NFT + SSI
Another week of rapid developments in the ecosystems surrounding Decentralized Identifiers and Verifiable Credentials
Welcome to Identosphere
Thanks to our Patrons
We appreciate your support. Each contribution brings us closer to covering our costs, keeps the newsletter free, and free from the influence of advertisment.
April Fools
DID Identity UN-DID Method Specification
A few week ago we shared about the DID:DID method. April Fools!! DID:UN-DID is another method in the series.
did:un-did is a DID method that enables using any valid Decentralized Identifier (DID) as a did:un-did DID, but more importantly it un-does the did that did:did did method performs.
Coming Up
Internet Identity Workshop XXXII (#32) • April 20-22 <—Register NOW. This is the main event for the whole community. The best place to dive in and get connected. 20% discount code: Identosphere_IIWXXXII_20
Credentials, COVID-19, and Digital Staff Passports Innovating and lessons from the NHS frontline • Wednesday, Apr 28
OpenID Foundation Virtual Workshop • April 29
PoCathon by Affinidi • 3\26–5\09
We invite developers across the world to come and build applications that generate secure, portable and privacy-preserving credentials enabling trust across entities using Affinidi’s APIsRedefining the Student Journey and Beyond Through Verifiable Credentials Condatis • May 11
Identiverse 2021 • June 21-23 (Denver)
MyData
Hidden in Plain Sight — the Transformational Potential of Personal Data MyDex
Personal data stores apply the same economic logic to transform the costs of producing data driven services. Verified attributes are the digital equivalents of Henry Ford’s standardised parts. By enabling one organisation to instantly re-use data verified by another organisation they eliminate the need for vast amounts of duplicated effort
COVID-19
The Politics of Vaccination Passports Windley
Social convention, and regulation where necessary, can limit where such a passport is used. It’s an imperfect system, but social systems are.
ToIP Foundation Hosts the Interoperability Working Group for Good Health Pass
The nine drafting groups collaborating within the new Working Group are:
Paper Based Credentials will define how a paper-based alternative can be created for any digital health pass so access will be available to all.
Consistent User Experience will specify the common elements required so that individuals can easily, intuitively, and safely use digital health pass implementations.
Standard Data Models and Elements will determine the core data items needed across all digital health pass implementations for both COVID-19 testing and vaccinations.
Credential Formats, Signatures, and Exchange Protocols will specify the requirements for technical interoperability of Good Health Pass implementations.
Security, Privacy, and Data Protection will define the safety requirements for Good Health Pass compliant implementations.
Trust Registries will specify how verifiers can confirm that a digital health pass has been issued by an authorized issuer.
Rules Engines will define how digital health pass apps can access different sources of policy information to determine what test or vaccination status is needed for a specific usage scenario.
Identity Binding will specify the options for verifying that the holder of a digital health pass is the individual who received the test or vaccination credential.
Governance Framework will define the overall set of policies that must be followed for an implementation to qualify as Good Health Pass compliant.
Provocative
Decolonial Humanitarian Digital Governance Berkman Klein
Can humanitarian digital policy be decolonized?
As humanitarian organisations do not tend to traditionally have the requisite digital or technology expertise in-house, they partner externally to achieve their aims.
The provocations:
What if shared well-being became the standard of success for our nations?
Are we ready to move from an era that rewards extraction to one that prioritizes regeneration?
How will we move from an era of destabilizing information into an age of trusted wisdom?
Can we dismantle industrial-age silos between work, home, education, play, and community?
SSI News!
ARUCC is pleased to announce a partnership between Digitary, its service partner, and MATTR, a friend of MyCreds™.
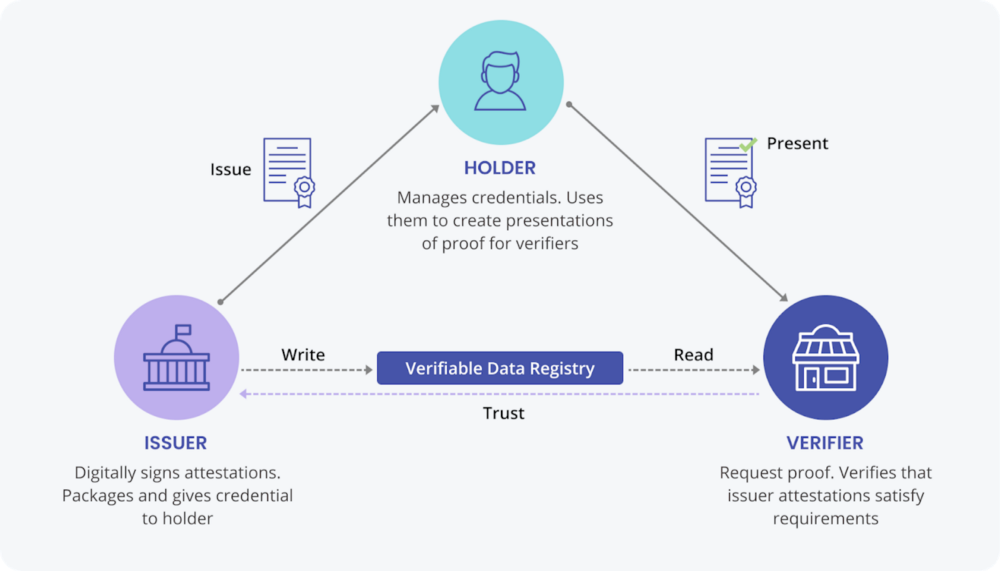
These two international organizations are combining their talents to deliver SSI (self-sovereign identity) and Verifiable Credentials for the ARUCC MyCreds™ virtual wallet. […] creating a triangle of trust that includes them and the Canadian colleges and universities.
Introduction to the future of identity - DIDs & VCs
I will show you how you can issue your own DIDs and VCs using the new Microsoft service in future blogs. This series' final blog will look at how DIDs can be anchored in decentralized transaction ledgers using ION and the Bitcoin blockchain.
Decentralzied Mapping Initiative – DIF Interop WG
eSSIF-Lab’s ecosystem: 2nd batch of winners: Infrastructure Development Instrument
another 7 proposals selected, out of 29 that were submitted before the second deadline of the Infrastructure-oriented Open Call
DIF Monthly #17 (April, 2021)
groups are preparing sessions and demos for IIW, Steering Committee elections are just around the corner, a whole hackathon kicked off organized by a member organization and devoted in large part to building on DIF specs and libraries
NFTs and the need for Self-Sovereign Identity Gimly
to verify the origin and legitimacy of an NFT and its linked object, and we invite you to join Gimly and bitcoin artist Petek @RaydarRayne on our journey to fulfill the potential of NFTs for digital and physical artists alike.
Social.Network, decentralized social media to launch first phase of its protocol on April 22nd
interested users will be able to create a self-sovereign identity on the platform by following the steps on the social.network landing page (h/t @SelfSovID)
Sidetree Protocol reaches V1 DIF
four of its implementers have been collaborating intensively for over a year on expanding and extending this specification together.
GATACA joins EU Commission’s Early Adopters Program as SSI provider in the Spanish group
three universities will pioneer the issuance of digital Academic Diplomas. The issuance will be performed 100% online, where students will authenticate themselves using a digital ID previously issued by FNMT (the Royal Mint of Spain) and stored in their mobile wallets.
Pan-Canadian Trust Framework (PCTF) – Overview
we are alpha testing the framework with different kinds of actors, both public and private, and with assessors. Through this process, we’re going to learn what may need to change, and what may not need to change.
Reimagining Customer Loyalty Programs With Verifiable Credentials: A Pravici Case Study Evernym
Their solution, Tokenized Loyalty Points (TLP), uses verifiable credential technology to give individual consumers control over their data, while empowering them to direct how their favorite brands can use this data for loyalty and other campaigns.
26 Suggested Use Cases of Verifiable Credentials (With Some Real-World Examples)
we hope that business leaders, entrepreneurs, and developers will use this article as a guide to create some breakthrough solutions that will benefit the society at large.
Layering Digital ID on Top of Traditional Data Management HIP
As concerns over data security, protection, and sharing mount, humanitarian agencies are being called upon to look to digital ID solutions as a potential response.
Takaways from the Suez Canal Crisis Karyl Fowler
Appeal for Supply Chain Agility — Powered by Verifiable Credentials
The Suez Canal debacle had a massive impact on global supply chains — estimated at >$9B in financial hits each day the Ever Given was stuck, totaling at nearly $54B in losses in stalled cargo shipments alone.
Webinar Series: rlogin Developer Workshop from RIF Identity Video (1:30:00)
rLogin allows web application developers to integrate blockchain technologies giving the user the power of data portability. After integrating rLogin you achieve:
- A back-end authenticating users by their wallet addressed - their Decentralized Identifiers.
- A registration model capable of requesting users for data stored in its user-centric cloud storage, the Data Vault.
- A front-end capable of interacting with any wallet that the user chooses, with a pre-designed user experience for registration and login.
- Compatibility with a unified platform where the user can control their identity and information, the RIF Identity Manager.
OAuth 2.0 meets VCs + ETH [slides] Sophie Project
SSI Orbit
A new podcast in town
Economics of Self-Sovereign Identity and the Future of Cryptoeconomics with Stepan Gershuni
The Importance of Data Inputs and Semantics for SSI with Paul Knowles
Patient-Centric Identity Management for Healthcare with Jim St-Clair
Identity not SSI
How to Sign Users In with IndieAuth Aaron Parecki
IndieAuth is an extension of OAuth 2.0 that enables an individual website like someone's WordPress, Gitea or OwnCast instance to become its own identity provider.
W3C WebAuthn V2 Now a Standard Mike Jones
user verification enhancements, manageability, enterprise features, and an Apple attestation format. (Recommendation) (CTAP also approaching standardization).
Financial-grade API (FAPI), Explained by an Implementer OpenID
Federated Identity, InCommon, and Enabling Federated Access to Research Services
review the concepts of federated identities, authentication, and the role attributes play in managing access to services. They’ll further describe how the InCommon Federation and eduGAIN enable academic collaboration across local, regional, national, and international scales
US latest to ensure immediate health record access
The US now requires healthcare providers to give patients access to all the information in electronic health records without charge.
The recent regulation change makes it the latest in a growing line of countries to give patients full online
MFA With WebAuthn for FIDO Device Biometrics Now Available
We are now announcing support for FIDO Device Biometrics for MFA using WebAuthn. This makes the security and convenience of WebAuthn-powered flows available to anybody who has a device and browser who can support the biometric challenge
Apple presses to replace paper passports and ID with iPhone
[This patent application] describes embodiments in which a person may present identification information through a mobile device instead of presenting a traditional form of identification
New Pages on Decentralized-ID.com
Covid Credentials Initiative • Podcasts • GLEIF • URSA • ID2020 • IOTA Foundation
Thanks for Reading!
Our Patrons help make this publication a joy to create!
You can support Identosphere on Patreon.