Identosphere 38b • Delegation Patterns • VC Lifecycle • Digital Colonialism
In part two of this weeks updates, you'll find all the standards work, Identity (not SSI), and Mydata related content!
This weeks updates were so voluminous we decided to split the digest into 2 parts as an experiment. Be sure to catch part 1 (38a) in your mailbox if you haven’t already!
Standards Work
Common Delegation Patterns in the Verifiable Credential Ecosystem Kyle Den Hartog
did you know that there are three ways in which you can utilize VCs and DIDs to enable delegation and attenuated delegation for more complex scenarios?
Bloom donates WACI
At its core, WACI can be thought of as a handshake using classic, industry-standard JWTs: the “Relying Party” signs a token given to the end-user’s wallet, and the wallet signs over a “challenge” contained within it, proving ownership of a DID.
The Verifiable Economy: Fully Decentralized Object (FDO) Example: Bob’s UDID Document
Strongly-typed Code to Generate Bob’s UDID Document
The VC Lifecycle Credential Master
In 1956 the switch to consistent shipping containers began, and it changed the physical world profoundly; the switch to consistent, authenticatable digital data containers will do the same for cyberspace.
Literal Digital Colonialism : AR overlays on the real world.
Geo Web is connecting digital content to the physical world with NFTs and Ceramic
With DID:NFT, because the content that is anchored to a Geo Web parcel can actually be owned by the parcel itself, when someone buys the land they're also getting the infrastructure that's been built up on that land.
Cardea Project Video
There are five agents main agents in the Cardea ecosystem. The health enterprise agent, which is a cloud agent that allows for a health organization a hospital lab clinic pharmacy. Whoever is going to be issuing the credentials to participate in hie would be a a government health organization all of those would be represented by a health enterprise agent issuing credentials there's a government agent that's represented in the ecosystem right now that verifies credentials presented to it and then issues trusted travelers a mobile verifier agent
Sigh- reinventing ZCaps…. Lightweight Credentials for Offers with UCAN
these are the types of use cases that we think can be created and enabled across the web as an open, interoperable standard. And some of it crosses into the work we're doing as part of the Decentralized Identity Foundation, too.
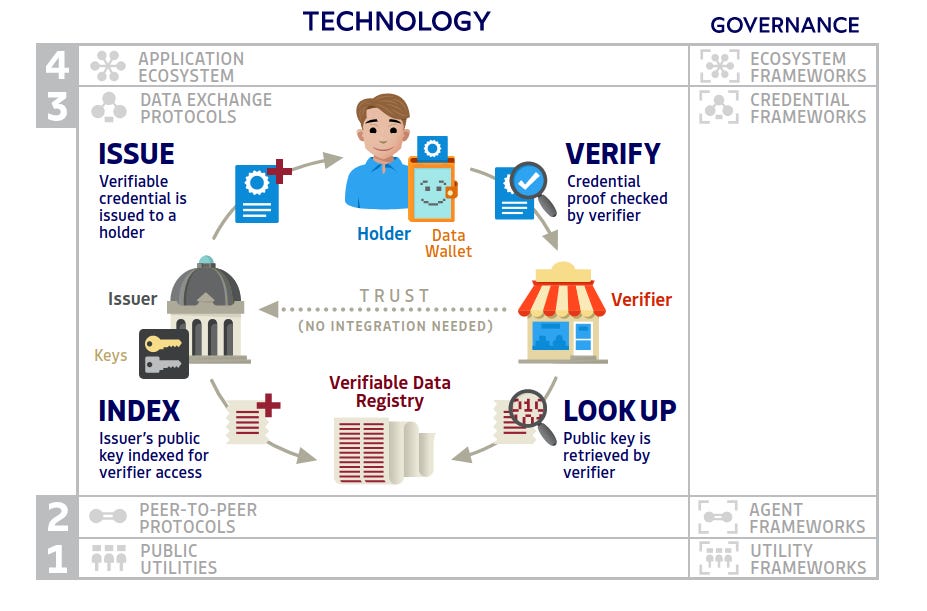
ToIP Primer
A history of procedural trust, leading to an overview of the TOIP stack.
ToIP Stack Diagram Preview
Interactive
Decentralized Identity FAQ DIF
SSI
Decentralized Identity opens the doors for safe travel and tourism Indicio
Machine readable governance enabled businesses and venues to trust that tourists had been tested on arrival by Aruba’s health department. Visitors using the digital Aruba Happy Traveler Card could be swiftly and reliably verified with a phone app. This freed both businesses and the government from the burden of mechanically collecting data with the attendant risk of error or fraud.
Empowering humans for a digital age and global economy via Self-Sovereign Identity
based on the article Self-Sovereign Identity in a Globalized World: Credentials-Based Identity Systems as a Driver for Economic Inclusion by Fennie Wang and Primavera De Filippi.
Growing confidence is programmed in – how self-sovereign digital identities make business relationships easier Bosch
Bosch will now also systematically transfer the self-sovereign identity (SSI) principle to the B2B sector – in other words to business relationships between companies. A further step will involve transferring it to secure and trustworthy interactions between machines.
Decentralized Digital Identity: Shaping the Future of Privacy Open Nodes
In May, Tribe held a Clubhouse session with the Dutch Blockchain Coalition (DBC), in partnership with the Singapore Infocomm Media Development Authority (IMDA). Together with representatives from Affinidi, SITA, and Sphereon, the industry players shared their insights on how blockchain is being used to shape the future of privacy, and some practical applications of decentralized digital identity.
KERI has a new website
Identity Not SSI
Kantara Initiative Names New Executive Director
Kay Chopard has been named Executive Director of the Kantara Initiative. She takes over the position from long-time Kantara Executive Director, Colin Wallis, who is semi-retiring. Kantara is the international ethics-based, mission-led non-profit industry ‘commons’ whose mission is to grow and fulfil the market for trustworthy use of identity and personal data.
A 21st Century Cures Act Security Primer Ping
health information must be accessible via an API, the API implementation must be documented, and that documentation must be made publicly accessible. The API provides access to highly sensitive health information that must be kept confidential and secure under federal and state privacy and security rules
Second Version of FIDO2 Client to Authenticator Protocol (CTAP) Now a Standard
The FIDO Alliance has completed the CTAP 2.1 Specification. This follows the publication of the closely-related second version of the W3C Web Authentication (WebAuthn) specification.
Notice of Vote for Proposed Implementer’s Drafts of Two FAPI 2.0 Specifications
OpenID Financial-grade API (FAPI) Conformance Tests Released for Final FAPI 1.0 Parts 1 and 2 Specifications
World’s Largest Tech Companies Drive FIDO Alliance’s New User Experience Guidelines
FIDO Alliance’s ultimate goal is to see as many service providers moving their customers away from password-based authentication as soon as possible – and we hope that these UX guidelines can help accelerate this movement.
FIDO2 Enhancements for Enterprise & Complex Security Applications
six major improvements that we are announcing today:
Enterprise attestation
Cross-origin iFrame support
Support for Apple Attestations
Better biometric management
Large blob support
Resident credential improvements
Always Require User Verification
Authenticate Virtual Summit: Focus on Europe Recap Fido Alliance
Technical
Example Design of an Authorization System with Verifiable Credentials and the Tradeoffs Kyle Den Hartog
The primary focus of this blog post is to highlight the different problems that are likely to occur when going down the path of building an authorization system with verifiable credentials. I’ll be sure to keep things at a higher level so that anyone can understand these tradeoffs, but take you through the details that would be thought through by an architect designing the system.
Gordian QR Tool Supports Vaccine Records, 2FAs, Cryptoseeds, and More Blockchain Commons
Some possible architectural issues arise from using QR codes for confidential data, such as the fact that you’re actually transmitting the data (not a proof of the data), that the QRs tend to contain all of the data (not just a selection), and that there’s no way to rescind a QR or expire it. Those issues will have to be dealt with at a foundational level as we figure out what can safely be encoded as a QR — and more importantly how to offer restricted proofs rather than complete information.
Most Common Security Threats to Mobile Devices in 2021
Mobile Application Security Threats. Application-based threats happen when people download apps that look legitimate but actually skim data from their device. Examples are spyware and malware that steal personal and business information without people realizing it’s happening.
Web-Based Mobile Security Threats. Web-based threats are subtle and tend to go unnoticed. They happen when people visit affected sites that seem fine on the front-end but, in reality, automatically download malicious content onto devices.
Mobile Network Security Threats. Network-based threats are especially common and risky because cybercriminals can steal unencrypted data while people use public WiFi networks.
Mobile Device Security Threats. Physical threats to mobile devices most commonly refer to the loss or theft of a device. Because hackers have direct access to the hardware where private data is stored, this threat is especially dangerous to enterprises.
How the trend of On-Demand Culture in the UK fuels the need for Digital ID Verification
Given that 85% of internet users in the United Kingdom would rather access the internet via a smartphone, digital ID systems that are accessible on both web and mobile platforms will be considered on-demand compliant.
MyData
MyData Global Joins “Team Data Spaces” to Support the EU’s Plan to Create “Data Spaces”
MyData Global announces to have joined forces with ‘Team Data Spaces’ – a coalition of leading European players with experience in standardising, creating and operationalising data sharing – to facilitate the development of European data spaces which are at the heart of the EU’s data strategy.
Support Centre for Data Sharing interview with Meeco
Meeco’s inception, its work so far and recent growth. Some of the the exciting projects discussed include mIKs-it, the safe multimedia app for children, developing a decentralised identity and verifiable credentials wallet and how innovators like VELA Solutions are transforming workforce management and My Life Capsule are helping their customers be prepared for a family emergency.
Thanks for Reading!
Let us know what you think
about the 2 part newsletter in the comments.
Should we be more selective and only send you the cream? or have tiered subscriptions and make people join patreon for the ‘deep cuts’?
Read more \ Subscribe @newsletter.identosphere.net
Support this publication @patreon.com/identosphere