Identosphere #54 • NFT, VC & PICO • Data Privacy Floor • Challenges to SSI
A weekly publication following the leading news in decentralized identity standardization, governance, education and development.
This weekly newsletter is possible thanks to Patrons, like yourself.
Just over a year since this weekly review began. Incredible! Thanks for sticking with us!
Consider paying us a small amount each month via Patreaon
Support our work on Patreon — Get Exclusive Content!!
Read previous issues and Subscribe : newsletter.identosphere.net
Contact \ Content Submissions: newsletter [at] identosphere [dot] net
Upcoming events
Self-Sovereign-Identity & eIDAS a contradiction? Challenges and chances of eIDAS 2.0 University of Murcia/Alastria 10/19
The Business Models Made Possible By Economic Incentives 10/19
Authenticate Virtual Summit Recap and looking forward Authenticate 2021 • 10/18-20 • Fido Alliance
Game Changers - Is Self-Sovereign Identity Going Exponential? 10/26
Does the W3C Still Believe in Tim Berners-Lee’s Vision of Decentralization? Evernym 11/3 (register)
Last month, Google, Apple, and Mozilla lodged formal objections to W3C approval of the W3C Decentralized Identifiers (DIDs) 1.0 specification.
Engineering Successful IAM Projects to Support Digital Business 11/23 KuppingerCole
Explainers
What is Self Sovereign Identity Florian Strauf
Decentralizing Identity - Taking Back Control Madigan Solutions
Self-Sovereign Identity allows individuals to manage their own identities by moving physical credentials to digital devices. An individual will receive a credential from an issuer which will be stored in their digital wallet.
The Sovereignty Stack: Re-thinking Digital Identity for Web3.0 w/ Greg KIDD [METACO TALKS #23]
In his latest venture Global ID, Greg is acting on his long-held belief that people’s identity should be truly portable and owned by individuals themselves rather than corporations or governments.
Standards Work
OIDC with SIOPv2 and DIF Presentation Exchange Sphereon
Sign in with Ethereum is being developed by Spruce
Already used throughout web3, this is an effort to standardize the method with best practices and to make it easier for web2 services to adopt it.
Why Are DIDs The Future of Digital Identity Management?
Why would you have 75 logins when you could have 1?
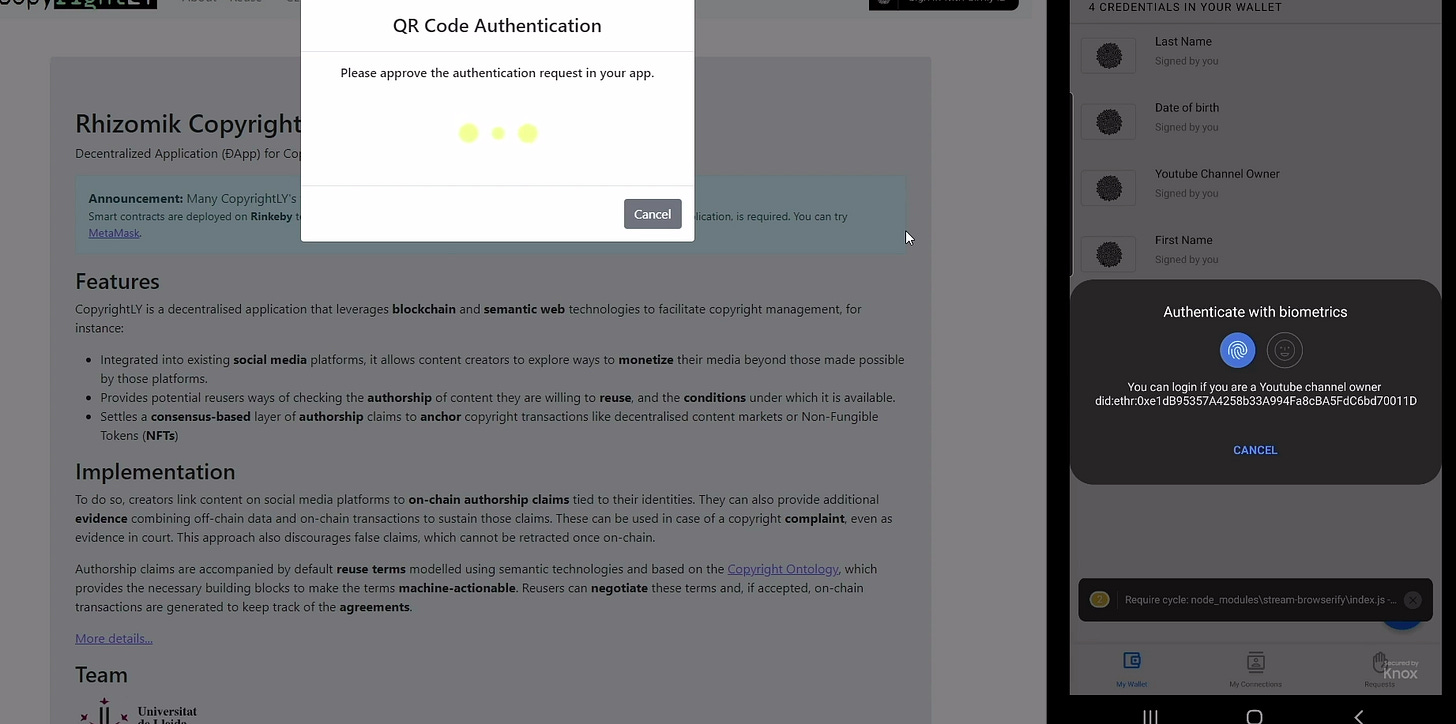
Gimly ID: SSI with OpenID authentication
About Dick Hardt’s new thing
Gimly ID is leading self-sovereign identity innovation, with the implementation of SSI with self-issued openID provider (SIOPv2) and full support for openID connect and DIF presentation exchange.
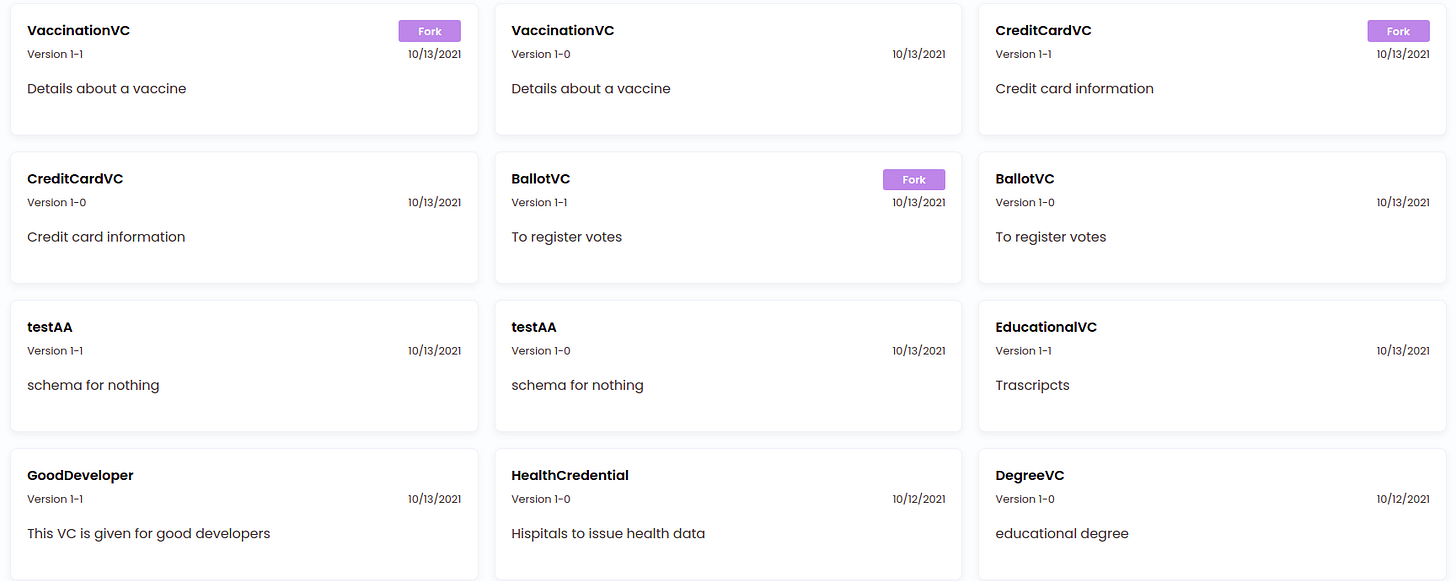
Explore Affinidi Schema Manager
Proof-of-possession (pop) AMR method added to OpenID Enhanced Authentication Profile spec Mike Jones
I’ve defined an Authentication Method Reference (AMR) value called “pop” to indicate that Proof-of-possession of a key was performed. Unlike the existing “hwk” (hardware key) and “swk” (software key) methods [...] Among other use cases, this AMR method is applicable whenever a WebAuthn or FIDO authenticator are used.
https://openid.net/specs/openid-connect-eap-acr-values-1_0-01.html
https://openid.net/specs/openid-connect-eap-acr-values-1_0.html
OpenID Connect Presentation at IIW XXXIII Mike Jones
Introduction to OpenID Connect (PowerPoint) (PDF)
The session was well attended. There was a good discussion about the use of passwordless authentication with OpenID Connect.
NFTs, Verifiable Credentials, and Picos Phil Windley
Summary: The hype over NFTs and collectibles is blinding us to their true usefulness as trustworthy persistent data objects. How do they sit in the landscape with verifiable credentials and picos? Listening to this Reality 2.0 podcast about NFTs with Doc Searls, Katherine Druckman, and their guest Greg Bledsoe got me thinking about NFTs.
Development
Clear is better than clever Cheney.net
“why would I read your code?” To be clear, when I say I, I don’t mean me, I mean you. And when I say your code I also mean you, but in the third person. So really what I’m asking is, “why would you read another person’s code?”
Survey Finds Customers Frustrated With Passwords, Open to Biometrics FindBiometrics
Passwords were a major point of contention in that regard, with a strong majority (68 percent) of consumers indicating that it is difficult to remember and key in a large number of passwords. Nearly half (44 percent) believe that biometric authenticators are easier to use, while 34 percent would prefer to use them as their primary means of identity
Ecosystem
These competitors joined forces to allow readers to use a single login across their news sites Nieman Lab
The founding media partners all agreed, however, that having more first-party data and increasing the share of registered visitors would allow them to build better relationships with readers and more relevant news products.
Self-sovereign identity use cases Cheqd
While self-sovereign identity (SSI) sounds like an unfamiliar concept for some, others are actively leveraging the technology to address industry-specific challenges — take the KYC trial of the Financial Conduct Authority or the IATA Travel Pass.
Challenges to Self-Sovereign Identity Damien Bod
I based my findings after implementing and testing solutions and wallets with the following SSI solution providers:
Different Wallets like Lissi
MyData Weekly Digest for October 15th, 2021
Data Co-Operatives through Data Sovereignty
[…] This article illustrates an open debate in data governance and the data justice field related to current trends and challenges in smart cities, resulting in a new approach advocated for and recently coined by the UN-Habitat programme ‘People-Centred Smart Cities’.
Public Sector
EEMA Training Launches with Focus on eIDAS, Self-Sovereign and National Identity, Blockchain, EU Legal Frameworks and Cyber Security
Everyone who takes part in a course will have been taught by those leading their respective fields. We do not believe this caliber of training can be found anywhere else.
The US Data Privacy Law “Floor”: What Deserves Basic Protections? Anonym
The New York Times recently did a deep dive into the United States’ lack of a national data privacy law
1. Data collection and sharing rights
2. Opt-in consent
3. Data minimization
4. Non-discrimination and no data use discrimination
IDnow AutoIdent will soon be usable according to German TKG
Automated identification procedures ensure seamless processes without media disruption and increase cost efficiency. By modernizing laws that allow these procedures, many cases can be simplified and modernized in the future.
DIDAS provides extensive commentary to the target vision for e-ID in Switzerland
Our submission (in German) is available here
The vital role of LEI Issuers in facilitating wider adoption of globally recognized business identities across Africa GLEIF
We spoke with Alberta Abbey, LEI Analyst, Data & Analytics, LSEG to discuss how this initiative will support wider adoption of globally recognized business identities, in the form of Legal Entity Identifiers (LEIs), across Africa and how to encourage more entities across Africa to obtain LEIs.
Use Cases
On solving the worldwide shipping crisis Doc Searls
“The supply chain is essentially in the hands of the private sector,” a White House official told Donna Littlejohn of the Los Angeles Daily News, “so we need the private sector…to help solve these problems.” But Biden has brokered a deal among the different stakeholders to end what was becoming a crisis.
It's been 15 years of Project VRM: Here's a collection of use cases and requirements identified over the years rebooted
I categorize them by the stage of the relationship between customer and vendor:
Category 1: Establishing the relationship
Top 5 Most Interesting NFT Use Cases (Part 1) Europechain
From racehorses to virtual sushi: a dizzying NFT panoply
The Future of Healthcare Relies on Adaptation auth0
Information security and identity management is not their core business, yet is a critical factor in compliant, secure business operations.
TrustBloc - Duty Free Shop use case (CHAPI Save + WACI Share)
This video demonstrates the TrustBloc platform to Issue a W3C Verifiable Credential through CHAPI and Share the Verifiable Credential/Presentation through WACI.
Governance
Battle of the Trust Frameworks with Tim Bouma & Darrell O’Donnell Northern Block
Levels of Assurance (LOA)
The Concept of Trust
The World of Trust Frameworks
The Importance of Open Source for Trust Creation
Personal Data
XSL Labs: Your Data Belongs to You
The SDI maintains to keep the practicality of a unique identifier while guaranteeing the security of the data and the user's sovereignty over it.
Portpass app may have exposed hundreds of thousands of users' personal data
The federal privacy commissioner also said it has not yet received a report, and said it has contacted Portpass to seek further information in order to determine next steps, and that it is in communication with its provincial counterpart.
Company News
Building towards a decentralized European Data Economy: A Minimal Viable Gaia-X (MVG) Ocean Protocol
Gaia-X is the cradle of an open, transparent, decentralized digital ecosystem, where data and services can be made available, collated, shared, and monetized in an environment of trust. More than 300 organizations and over 2500 contributors are already supporting Gaia-X.
Node Operator Spotlight: Anonyome Indicio
Each of the capabilities of the Sudo Platform is attached to a persona. This includes masked email and masked credit cards, private telephony, private and compartmentalized browsing (with ad/tracker blocker and site reputation), VPN, password management, decentralized identity and more.
Okta + Auth0 Showcase 2021: Identity for All
Cloud, mobile, and Bring Your Own Device (BYOD) have transformed the dynamics of the digital world over the past decade. At the same time, IT is struggling to keep up with all of these changes, and developers are more burdened than ever
Auth0 Identity Platform Now Available on Microsoft Azure
secure cloud deployment option for organizations seeking strategic fit with their technology stack, supporting regional data residency capabilities and higher control over customer data.
Introducing: Civic Pass Integration Guide
developers can plug Civic Pass into their platform and create an identity layer that allows for a permissioned dApp platform, be it a DEX, an NFT marketplace or mint, a metaverse
Equifax Launches Digital Identity as a Service CU Ledger
Equifax’s suite of identity protection products including Digital Identity Trust, Document Verification and the recently acquired Kount Identity Trust Global Network are incorporated into the new holistic solution.
How Yoma Uses Trinsic to Help African Youth Build Digital CVs
Verifiable credentials is a beautiful set of technology that allows people and organizations to get the data in a verifiable form that still respects agency
WAYF certificeret efter ISO 27001
WAYF has now been certified according to the standard for information security ISO 27001.
Bloom OnRamp Has Arrived
Beyond OnRamp’s direct data integrations, the platform also supports the ability for third party credentials to enter the OnRamp platform via the WACI specification
Decentralization
GiD Report#181 — The future will be self sovereign
Just as the World Wide Web empowered people to connect and share knowledge and information, the rise of Bitcoin taught us that we could have direct ownership over our valuable assets and payments — no middle man or central operator necessary.
ID Not SSI
There’s No Distributed Ledger Technology (DLT) in X-Road
All the nodes of an X-Road network have their own sequence of transactions that are not shared with any other nodes – not even in a Security Server cluster. Therefore, there’s no need for a consensus algorithm in X-Road.
Thanks for Reading!
Read more \ Subscribe: newsletter.identosphere.net
Support this publication: patreon.com/identosphere
Contact \ Submission: newsletter [at] identosphere [dot] net