Identosphere 81 • Apple Google & MS to expand support for FIDO • ISO/IEC 18013-5 vs SSI • DID:INDY complete!
Weekly edition of news and updates surrounding decentralized id, data sovereignty, relevant public policies, events and other updates!
Welcome to Identosphere’s Weekly!
✨✨✨Thanks to our newest patrons✨✨✨
Support Identosphere on Patreon …or reach out to Kaliya directly.
Read and Subscribe : newsletter.identosphere.net
Submissions: newsletter [at] identosphere [dot] net
Upcoming
MEF CONNECTS Personal Data & Identity 5/10-11 Mobile Ecosystem Forum (Kaliya will be there both days)
European Identity & Cloud Conference celebrates its 15th edition Berlin - 5/10-13 (Kaliya will be there 12-13)
Kaliya thinking of hosting a social conversation in London likely on May 17th at NewsSpeak House - you can register on eventbrite.
Complex harms reduction through co-design of socio-technical systems in FinTech HXWG May 18th TOIP
Travel & Hospitality Biometrics Online Summit FindBiometrics 5/28 (register)
ID4Africa Marrakesh, Morocco 6/15-16 (Kaliya will be there in advance of the conference starting June 11 through the 17th)
IAM and SSI: A Combined Approach to Digital Identity June 15th, 2022 TOIP
Kaliya hosting a meetup in the Netherlands on June 18th details TBD - reach out if you want to help her organize it.
Identiverse in Denver June 21-24, 2022 (Kaliya is talking there)
Thoughtful Biometrics Workshop - Mid July virtual several days over 2 weeks.
Decentralized Web Camp August 24-28 in Northern California (Kaliya will be attending and encourages SSI folks to participate)
Internet Identity Workshop #35 November 14-16, Mountain View California
Policy
End-To-End Encryption is Too Important to Be Proprietary Cory Doctorow
End-to-end messaging encryption is a domain where mistakes matter. The current draft of the DMA imposes a tight deadline for interoperability to begin (on the reasonable assumption that Big Tech monopolists will drag their feet otherwise) and this is not a job you want to rush.
Explainer
Podcast: Digital Identity and Self Sovereignty Kaliya Young & Lucy Yang -Future of You
The tools Kaliya and Lucy are developing to enable self-sovereign identities
Whether anonymity or pseudonymity is feasible while maintaining accountability
Wallet Wars: how might wallets evolve and consolidate across the public and private sector
Decentralization is the Future of Digitization Jolocom
Digital identity data is introduced as having a positive impact on Germany’s future as well as Europe’s. Following, benefits of a decentralized identity based on a fully open infrastructure are given.
What Will We Learn from the Market Failure of Digital Identity? Identiverse
We have a widely accepted Standard Model of Identity, or architecture, in which Subjects, Identity Providers and Relying Parties (aka Holders, Issuers and Verifiers) hold, present, exchange, use and/or consume digital identities.
The World’s First Verifiable Credentials Steve Wilson
Commonly associated with blockchain and the Self-Sovereign Identity movement, Verifiable Credentials are in fact an old idea. It is instructive to break down their essential properties and examine the pioneering examples.
Standards Development
Me2B Safe Specification v1.0 Me2B
The current version focuses on mobile apps and websites and encompasses only a portion of the harms outlined in the complete Me2B Digital Harms Dictionary. As the safe specification evolves subsequent versions will grow to include more of the harms identified in the Me2B Digital Harms Dictionary.
Building a Safety Spec for the Digital World Me2ba
It was three years in the making, and this is how we got here.
A WebAuthn Apache module? Hans Zandbelt
any sensible WebAuthn/FIDO2 Apache module would rely on an externally running “Provider” software component to offload the heavy-lifting of onboarding and managing users and credentials.
ONT ID Upgrade: Verifiable Credentials SDKs Now Open Source Ontology
In making the code widely accessible, Ontology is accelerating the adoption of decentralized identity (DID) in the blockchain sphere As the project that has focused on the Decentralized Identity (DID) field for over 4 years…
Agri-Food Product Identity Verification & Governance DIACC Special Interest Group Insights
This report discusses what the identity verification related requirements for the creation and management of agri-food products (or items) unique identifiers to enable provenance tracking, ensure traceability, facilitate agri-food data integration, enhance governance, protect privacy and confidentiality, inform policies, and improve communications.
ISO/IEC 18013-5 vs Self-Sovereign Identity: A proposal for an mDL Verifiable Credential Procivis
in the context of government identity programs we see it as useful to compare them on the following parameters – background, credential data model & trust anchor and transmission protocols.
Hyperledger completes development of DID:Indy Method and advances toward a network of networks Howland & Bluhm - Linux Foundation
With the groundwork complete, networks and agent frameworks now need to incorporate the Indy:DID Method. This community adoption will increase the viability of the Indy and Aries project stack and position it to be the globally dominant way to issue and share verifiable credentials in a multi-ledger world.
Company News
Remittances Specialist Leverages Biometric Onboarding Via Onfido Find Biometrics
Chipper Cash has become the latest financial institution to adopt Onfido’s identity verification technology. The company currently operates one of the largest money transfer platforms in Africa, and is hoping
Spruce Developer Update #19
Sign-In with Ethereum offers a new self-custodial option for users who wish to assume more control
Kepler is a decentralized storage network organized around data overlays called Orbits. Kepler allows users to Securely share their digital credentials, private files, and sensitive media to blockchain accounts, all using a Web3 wallet
What Indicio’s Seed Funding Means for Decentralized Identity Technology Indicio
Our new funding will be used to refine the open-source, decentralized-identity technology stack. We have the basic technology for a functional ecosystem, now we improve that functionality by adding all the features, user interfaces, and management tools that make it easier to deploy, use, and monitor.
Raising the Bar on Identity: One Year of Okta + Auth0
Today marks one year since Okta and Auth0 officially teamed up to lead together in the customer identity and access management (CIAM) market.
Exposing Bad Actors Who Hide Behind Anonymity With Traceable Credentials Dock
Traceable credentials are a way of instilling that layer of privacy but allow the relevant authorities to ‘unwind’ that layer of privacy and identify those bad actors. We do this through verifiable encryption.
final phase eSSIF-Lab and maximum funding by the European Commission Work X
our team has been selected to enter the third and final phase of the European Self-Sovereign Identity Framework Lab. [...] to let employees regain control over their career-related data. Therefore receiving the maximum development grant of €106.000
Expanding the public preview of verifiable credentials Ankur Patel Microsoft Identity
more than 1,000 enterprises with premium subscriptions have issued and verified tens of thousands of verifiable credentials […] from remote onboarding at work, collaboration across business boundaries as well as enabling education beyond the campus [...] we are extending the public preview […] for all Azure Active Directory (Azure AD) Free and Premium users.
Myth Busters
myths and facts. Is Self-Sovereign Identity Dangerous? Jolocom (in german)
we examine more closely whether self-sovereign identity can increase or reduce risks for data misuse in certain cases.
Digital Identity Conspiracies ContinuumLoop
The only ones who will benefit from your digital ID are the Issuer (who gave you the credential), holder (you) and verifier (who you’re sharing it with).
Data Managment
Helping Data Trusts Manage Personal Data Mydex
Mydex CIC has just published a blog for Cambridge University’s Data Trust Initiative on ‘Helping Data Trusts Manage Personal Data’. In it, we address the challenges that arise as the Data Trust movement begins to scale.
EDU/HR Use-Case
Self-Sovereign Identity User Scenarios in the Educational Domain Gerd Kortemeyer Educause
The model of self-sovereign identity offers tempting benefits as educational systems become increasingly global and as learning spans a lifetime.
Blockchains in HR: Prosoon and Talao go together on SSI and HR credentials Talao
This partnership will enable the use of Blockchain and Self-Sovereign Identity technologies such as verifiable credentials to enable the support of diplomas and professional certifications in compliance with personal data in a decentralized environment (#web3).
Wallets
Self Sovereign Identity through Thrivacy Wallet Dr Gordon Jones
“Blockchain Ethics: A Bridge to Abundance” (2018) and “Re-Generation X” (2020) not only discuss the benefits of blockchain technology, but also capture Jamil’s experience on how he has transitioned from being a loyal yet downsized former corporate employee to a self sovereign individual.
Trust In Your Wallet Findy Agency
Finnish Trust Network (FTN) consists of “strong electronic identification” providers. The concept means proving one’s identity in electronic services that meets specific requirements laid down by Finnish law. The identity providers are required to implement multi-factor authentication to authenticate the users.
.
Identity Not SSI
Apple, Google and Microsoft Commit to Support for Standard to Accelerate Passwordless Sign-In FidoAlliance
two new capabilities for more seamless and secure passwordless sign-ins:
Allow users to automatically access their FIDO sign-in credentials (referred to by some as a “passkey”) on many of their devices, even new ones, without having to re-enroll every account.
Enable users to use FIDO authentication on their mobile device to sign in to an app or website on a nearby device, regardless of the OS platform or browser they are running.
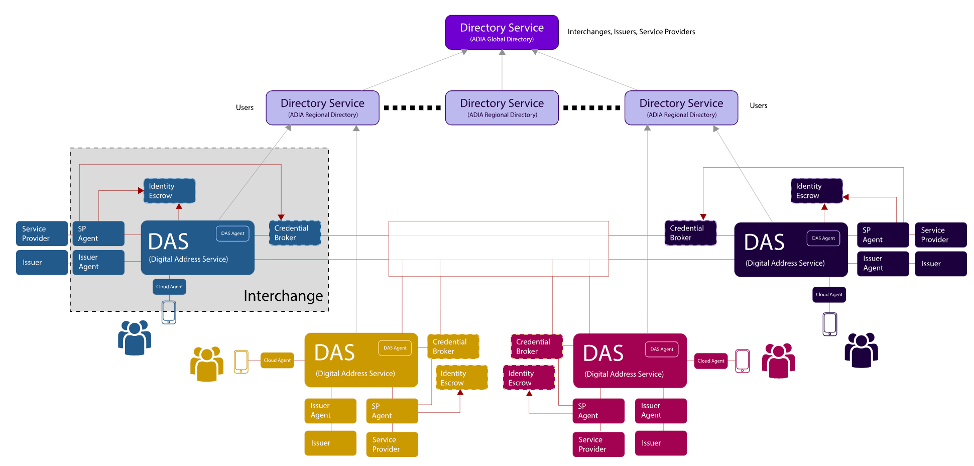
Accountable Digital Identity (ADI) Kiran Addepalli
In the last blog post, I presented a non-trivial use case where Verifiable Credentials can reduce process timelines and enhance digital transformation efforts for enterprises. I mentioned Accountable Digital Identity (ADI) as a framework for Trust and Accountability.
Editorial Note: The reason this is in Identity NOT SSI is because it does not follow the conventional SSI model and instead has a closed network of “core” identity providers that are let onto their network.
Web 3
Sign-in with Solana — Use Your Solana Account for Web2 & Web3
Users will now be able to control their digital identity with their Solana accounts instead of relying on traditional/custodial profiles. The Importance of Building a Self-Custodial Future In crypto, there is a saying that goes ”Not your keys, not your crypto’’
Web3Auth at the Paris Blockchain Week 2022 Torus
A whole lot of ecosystem players at the event were pleasantly surprised to discover Web3Auth’s Key Management Infrastructure
iXRPL - A Smart Contract-Powered, Self-Sovereign KYC Solution for the XRP Ledger by Scott Chamberlain, Richard Holland, and Ravin Perera
the verification is “stamped” on the User’s XRP Ledger Account with a Non-Fungible-Token, called a Human UUID, that uniquely identifies the verified individual. The User can then present their verified credentials, cross-checked against the XRP Ledger Account, to financial institutions to satisfy KYC requirements. Effectively, iXRPL “tokenises” the one-off cost of verifying your identity into a reusable asset.
7 Essential Ingredients of a Metaverse Liz Harkavy, Eddy Lazzarin, Arianna Simpson
Solving the ‘Sunrise Issue’ is the key to unlocking crypto mass adoption Cointelegraph
Regulation will touch every person in every jurisdiction worldwide; crypto must find ways to preserve its decentralization and privacy.
Question: Does SSI align with these?
FRIDA’S principles to guide data and technology Young Feminist Fund
The tech we use should be responsive to and responisble with the climate, environment crises of our time. Frida advocates for the use and creation of volence-free technologies putting first the care of our territories and bodies
They also published this - which is good for all in tech to think about
FRIDA Happiness Manifesto Young Feminist Fund
✨Thanks for Reading!✨
Read More \ Subscribe: newsletter.identosphere.net
Support this publication: patreon.com/identosphere
Contact \ Submissions: newsletter [at] identosphere [dot] net