Identosphere Weekly #10: MyData • VCs for LEI • oCap/ZCap on CCG
Dec 6-12 a busy week in identity, with MyData, a big announcement from GLEIF, and LOTS MORE
Thanks so much to our subscribers and everyone who’s sharing these posts!
Kudos to new patrons! We’ve got 3 more, this week, for a total of 12 people contributing a total of $107 per month.
Your support is much appreciated and provides extra incentive to make this the most comprehensive SSI newsletter around!
Contribute at patreon.com/identosphere
Upcoming Events
December 15 - ToIP & Government Webinar
December 16 - Open Meeting: Board of Trustees of the Sovrin Foundation
December 16 - Getting Started With Self Sovereign Identity - Conditis
MyData was this week!
It was fantastic. Kaliya was part of the opening plenary and organized a session about the Origins of Identity and participated in a session on Sustainable Self-Sovereign Agents.
They also have a post proposing Data Exchange Board to Improve the EU Data Governance Act
MyData Sessions
Scaling the personal data economy, MyData 2020
Florian Werner spoke about use-cases, equitable models for value exchange, and who to trust in facilitating the ecosystem and bringing stakeholders together.
Sari Stenfors takes us on a guided journey:
using Futures Thinking to envision how different business strategies, policies and actions implemented in the personal data ecosystem can pave the path towards the Desirable Future.
MyData Online Demo "Keep a Lifelog with Personium"
Before: Your personal data stored separately in the silos of various domain services…
After: Keep in one place and share easily. Then utilized by other apps and selectively disclosed to 3rd parties
Ada Lovelace Institute (ALI) Shares Highlights and References
discussing different approaches to data stewardship and potential principles individuals and organisations can follow
Exploring principles for data stewardship - case studies exploring principles for data stewardship - ALI
Data Trusts Initiative - interdisciplinary programme that pursues research at the interface of technology, policy and the law to better understand the role data trusts can play
Data Futures - Research to shift power through data governance - Mozilla Foundation
The Data Economy Lab - unlock the societal value of data while safeguarding the rights of individuals and communities.
Practising data stewardship in India, early questions - could data stewardship help to rebalance power towards individuals and communities? ALI
Doing good with data: what does good look like when it comes to data stewardship? ALI
@CjColclough shares: Towards Workers' Data Collectives (The Why Not Lab)
Written for Just Net Coalition and IT for Change Digital New Deal essay series
Crossing the Chasm for Privacy respecting Identity, MyData 2020
This is the most highly produced zoom presentation Infominer has ever seen:
Presenters: Nat Sakimura, Sheila Warren. Host: Kristina Yasuda.
1. Accountable Digital Being
2. Expressive Digital Being
3. Fair Handling of personal data
4. Right NOT to be forgotten
5. Human Friendly
6. Open, Interoperable, Leveraging Existing Infrastructure, and Tested
7. Everyone Benefits
Hopefully next week we’ll have found more of these excellent presentation materials
LEIs to enable corporate digital ID with verifiable credentials
The Global Legal Entity Identifier Foundation (GLEIF) is the umbrella body that delegates responsibility for issuing LEIs to local organizations.
It’s such a pressing issue that it was raised by the OECD and B20 (G20 business) just three months ago when they suggested a Global Value Chain (GVC) Passport.
GLEIF Press Release
Self Sovereign Identity-Land
Orie Steel Presents
Mental Models of JSON-LD and what a "Document Loader" really does
and terms like "dereferencing" that trip up even highly experienced senior developers that show up late to the Linked-Data party and its open-world model (complete with its own security model based on different availability assumptions).
Can’t say enough good things about BBS+ Signatures
Tobias Looker from MATTR presented BBS+ use-cases to the Interoperability working group at DIF:
Replay attack protection
Domain-specific identifiers and proofs
New partial-disclosure topographies
DIF Job Opportunities
…available for the following positions:
Backend Engineer
Director of Engineering
Frontend Engineer
Lead Solutions Architect SSI
Full-stack Engineer
Hands-on Architect
Head of Mobile Development
5 Promising Use Cases for Verifiable Credentials - Hackernoon
verifiable credentials promise to appear in our daily lives in the not-too-distant future.
In fact, several industries are already digging in. Here are some of the most visible and promising use cases.
EPS for SSI (Self-Sovereign Identity)
you might be interested to hear that the core of EPS is designed to convert images to high-entropy codes, which work as very long passwords and also as the seeds of symmetric or asymmetric cryptographic keys.
@lissi_id and the three-sided credentials market
When a user holds his:her own credentials locally on the phone, it creates a three-sided market, which puts the holder of the credential in the position of a carrier between issuer and verifiers.
Identity Credential and Personal Data Ownership Perspectives
Many global organisations are using their citizens’ identity and their other personally identifiable information (PII) to help combat the global Covid-19 crisis […] reignited the debate around protecting public safety vs protecting privacy: how to combat the contagious threat whilst preserving citizens’ digital identity, security and anonymity?
RIF’s Self Sovereign Identity Developer Library and Repos
@baselineproto Baseline Protocol office hours.
Events and Announcements! @jwolpert shares:
From CCG Mailing List
Epic VCs vs oCaps/ zCaps discussion
Begins with a post by Kaliya sharing a conversation including Manu and Sam Smith:
Below is the prior threads cut and paste. If you would rather read it in a document form that is attached.
Christopher Lemmer Webber followed up with an illustration using the analogy of hygiene to express separation of concerns between oCap and ZCap.
Hygiene for a computing pandemic: separation of VCs and ocaps/zcaps
You *could* implement zcap-ld on top of VCs…
However, you're actually squishing together what should be a separation of concerns in a way that will become *unhygienic*. Like a lack of proper biological hygiene, the result is sickness in our computing systems.
The observation of "these things seem so similar though!" is true, but you can already make that claim even if you're just looking at the linked data proofs layer. VCs and zcap-ld diverge from there for two very separate purposes: what is said, and what is done.
The Conversation split off a few times from there, you can browse threads here.
Re: VCs - zCaps / OCap a Discussion Dave Longley 12/5
TL; DR: My current view is that the main confusion here may be over the difference between VCs and LD Proofs, not VCs and ZCAPs. VCs are not a generalized container for attaching a cryptographic proof to a document. That's what LD proofs (or JOSE style proofs) are for. VCs *use* LD proofs (or JOSE style proofs) to attach an assertion proof to a document that specifically models statements made by an issuer about some subject, which is therefore inherently about the identity of that subject.
COMMUNITY BLOG POSTS
Distributed ID learning path
Christina Yasuda shares a learning path, based on her work navigating the VC-Spec Map by Michael Ruminer, that we shared a few weeks ago and has now been donated to the DIF.
Her distributed ID learning path first describes pre-requisite knowledge, including JSON, JSON-LD, JWT, JWS, JWK, JWA, and sometimes CBOR. She then goes on to break down knowledge areas beginning with the basics: DID-Core, DID-Resolution, DID-Spec, DID Use-Cases. Next, she covers Verifiable Credentials with VC-Data Model, VC Use-Cases, and VC-Implementors Guide, and also Transport, Credential Presentation, and Other Data Formats.
I Want COVID-19 Certificates but I don't want a DID
David Chadwick shares his talk from Kuppinger Cole's "Identity Fabrics & the Future of Identity Management"
The Mental Models of Identity Enabled by SSI
Adrian Doerk (@SSI_Ambassador) helps clarify how different perspectives can be all be found within the SSI systems/models/frameworks.
The Models: Space Time • Presentation • Attribute • Relationship • Capability
Another great post by Windley on the use of DIDComm
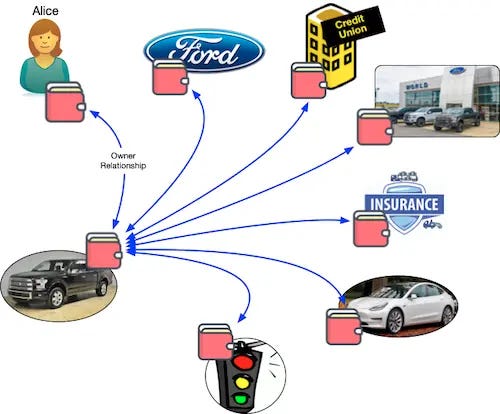
Relationships in the Self-Sovereign Internet of Things
This post looks at Alice and her digital relationship with her F-150 truck. She and the truck have relationships and interactions with the people and institutions she engages as she co-owns, lends and sells it.
The Dataweb: An Introduction to XDI
When I (Infominer) published the The Augmented Social Network on Decentralized-ID.com, a few weeks ago, @SelfSovID said:
One of the two most influential papers I've ever read.
The other was the 2004 vision for the XDI Dataweb by @drummondreed.
So I asked Drummond if it would be ok for me to also publish this paper, which I wasn’t already familiar with. So now you can read it there with on-page navigation
The Dataweb: An Introduction to XDI - “presents several examples of classic cross-domain data sharing problems, explains how the Dataweb model can provide a generalized solution”
Other Stories
Disability-inclusive ID Systems
Creating an inclusive ID system requires a comprehensive, whole-of-system approach to overcome barriers to ID enrollment and use for persons with disabilities.
Turing Institute Report on Trustworthy Digital Identity
Turing harnesses global expertise with International Advisory Board for Trustworthy Digital Identity
The ambition is to produce a definitive set of tested and accessible tools, best practice guidance, and design references based on six key criteria for assessing the impact on trust in national identity programmes: security, privacy, ethics, resilience, robustness, and reliability.
MOSIP makes the Economist
Covid-19 spurs national plans to give citizens digital identities
The MOSIP project, which got going in March 2018, is nested in Bangalore’s International Institute of Information Technology (IIIT-B) and endowed with funding of $16m from the Omidyar Network, the Bill and Melinda Gates Foundation and Tata Trusts.
News around the world
Public Sector Profile of Pan-Canadian Trust Framework
The Public Sector Profile of the Pan-Canadian Trust Framework Working Group Close-Out Report was published on Tim Bouma’s medium blog. I look forward to when this can align with the overall PCTF work of DIACC.
the PSP PCTF WG was an important vehicle for ensuring public sector communication and discussion across Canada
DIACC marks year end with a slideshow detailing their accomplishments
A few highlights from the report:
Digital Identity Laboratory - first lab of its kind for digital ID testing and certification
launched the COVID-19 Actions Directory highlighting member initiatives.
DIACC has joined the collaborative led by Standards Council of Canada
DIACC is also inviting input on the future of Levels of Assurance.
Making sure we have a common way to evaluate and measure the integrity of that data is central to a common bar of acceptance
Digital Identity New Zealand
DINZ held the first Aotearoa Digital Identity Hui Taumata
Bianca Lopes and David Birch shared with us their International perspectives and insights, including a whirlwind Identity world tour hosted by Bianca and her team at Talle.
Institutions and Governance in the digital realm of Africa
Omidyar Network:
seeking to better understand the existing laws and institutions
exploring ways to strengthen the capacity of institutions that uphold these laws
supporting digital rights organizations throughout Africa to act as checks on technological excesses of both governments and corporations
Europe’s top Data Portability Projects
ALIAS – automating GDPR portability for applications developers.
Checkpipe Charlie – tool for describing and validating data.
DIP – Vaccination & Immunization Management using Verifiable Credentials.
Domi – SSI-based digital passport to facilitate data portability in the housing rental sector.
DPella – Data analyses with privacy in mind.
IDADEV-P2P – Blockchain Based Data Portability System
OpenPKG – decentralised data provenance system for improved governance and portability of personal data.
OpenXPort – Open export of data across different systems and providers.
ORATORIO – Energy data exchange platform.
Prov4ITData – Provenance-aware querying and generation for interoperable and transparent data transfer.
UI-Transfer – complete solution for “user initiated inter-controller and continuous data transfer”
The European Single Identity System “Back to the Future”
What are the Pros and Cons? - ISSE 2020 Webinar 3 (Tim Bouma says to watch this)