Identosphere 22 • Okta Acquires Auth0 • Azure AD VCs Preview Soon • Tezos DID Method Draft
Weekly SSI updates on upcoming events, organizational announcements podcasts, videos, and Covid ID news
Welcome (Back) to the Identosphere Weekly
We scour the feeds so you don’t have to, delivering news and updates related to decentralized identity to your inbox, each week.
You can subscribe and read previous editions at https://newsletter.identosphere.net and support the creation of this newsletter on Patreon.
Coming up
Thoughtful Biometrics Workshop March 8,10,12
The Thoughtful Biometrics Workshop is creating a space to dialogue about critical emerging issues surrounding biometric and digital identity technologies.
Our inspiration for this event comes from the Internet Identity Workshop an event uses the open space technology to co-create the agenda live the day of the event.
Data Ownership and Self-Sovereign Identity by Cryptonics March 10th
how it works from a technical point of view to the different real use cases in the world we are living in. Timestamping, digital signature, e-voting, authentication, and private contracts are some of the key elements that would be explained during the session.
Internet Identity Workshop XXXII (#32) April 20-22
You’ll acquire the real-time pulse of genuinely disruptive technologies that are the foundation of today's important Internet movements.
Consumer Identity Management Evolution April 20, 2021
Busy that day? Register anyway & watch the recording.
Few businesses are evolving CIAM to deliver better security and privacy for customers as a way to differentiate their digital experiences from their competitors. Fraud reduction is another area where CIAM could boost customer experiences and brand loyalty. These are only a few of the CIAM opportunities
Registration - OpenID Foundation Virtual Workshop April 29, 2021
updates on all active OpenID Foundation Working Groups as well the OpenID Certification Program [...] also highlights the Foundation’s partnership with the CARIN Alliance that is focused on enabling a digital identity ecosystem for US healthcare and specifically the role of OpenID Connect and Connect certification in trust frameworks in Medicare and Medicaid. And Kristina Yasuda’s presentation on Self-issued OpenID Provider (SIOP) will include background on the Foundation’s collaboration with the Distributed Identity Foundation
Identiverse 2021 June 21-23 • Denver, co
Big News this week Outh0 was acquired by Okta!
These are two conventional IAM/CIAM companies joining. But, if you recall, two weeks ago we shared an interview with Okta’s CEO where he discussed SSI positively. It would not surprise us to see Okta acqui-hiring one, if not several, SSI companies in the (near?) future.
Okta + Auth0: Powering Identity for the Internet
I'd go so far to call it a "leap" — to enhance the Okta Identity Cloud. We announced our agreement to join forces with Auth0, a leading identity platform for developers.
Okta Signs Definitive Agreement to Acquire Auth0
Auth0 will operate as an independent unit inside of Okta, and both platforms will be supported and invested in. As a result, organizations will have a wider breadth of identity solutions to fit their unique needs. Okta and Auth0’s comprehensive, complementary identity platforms are robust enough to serve the world’s largest organizations and flexible enough to address every identity use case, regardless of the audience or user.
Kuppinger Cole Comment: Okta & Auth0
Why developer-first IAM ? And why Okta’s Auth0 acquisition matters? Prabath Siriwardena
Like Microsoft’s acquisition of GitHub for $7.5B in 2018, Okta’s acquisition of Auth0 for $6.5B is a win for developers!
Auth0: Our Commitment to You, Developers
Your Auth0 implementation will continue to receive the same support and services you have come to expect
Auth0 Names Jameeka Green Aaron as CISO
Leadership change announced before acquisition
“In addition to the amazing roster of customers that puts their trust in Auth0 and fuels its growth, I was very much struck by the humanity of everyone I met with—a level of empathy that has been a rarity throughout my career,” said Aaron
Continuous Access Evaluation Protocol (CAEP) with Tim Cappalli and Atul Tulshibagwale
Doesn’t cover the acquisition, but good.
Tim and Atul take turns in digging in the details of CAEP, its dependency on the Security Event Token specification (SET), and how its features are complementary with the ones defined by SCIM and FastFed
Videos and Podcasts
NGI Forward SALON ON DIGITAL SOVERIGNTY IN eID-Solutions2: Self-sovereign, Centralised or Privatised?
Without a clear vision on identity, society will have no agency since the capability to produce future value (data) is not under regional, nor national, nor international regulated control.
Therefore it is important to have a good overview of what is happening in different parts of the world to see if we can not combine innovative solutions.
Germany’s digital identity landscape with Verimi’s Roland Adrian
Roland fills us in on how Verimi works and its privacy-by-design cornerstones, including data minimisation. Oscar and Roland also discuss the digital identity landscape in Germany
Julian Wilson: Self-Sovereign Data meets Open Banking
Julian Wilson began his career at Apple in the late 80s [...] joined Ecospend in 2019 to build a self-sovereign data service on top of an Open Banking platform. He describes his role as putting an Internet lens onto product design.
Paper based Verifiable Credentials Mattr
Paper-based Verifiable Credentials allow us to have a low-tech solution for adopting VC's in situations where access to a phone cannot be guaranteed. This presentation looks at how this solution can be used to aid with the distribution of Vaccine Credentials.
Commentary/Thought Leadership
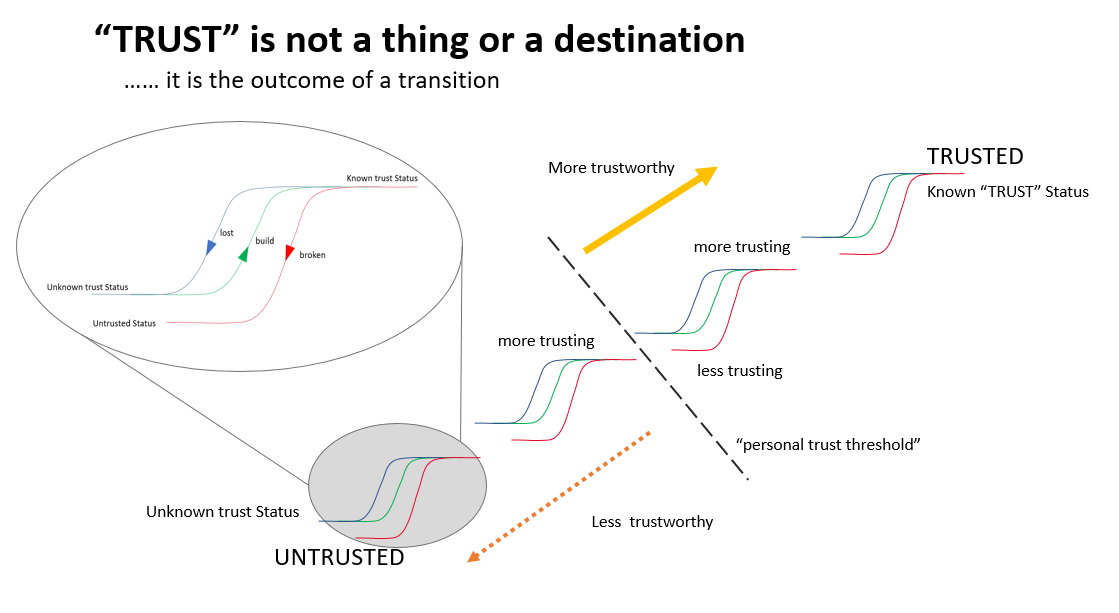
Trust is not a thing or a destination, but an outcome from a transformation
I say this all the time Trust is a feeling not a “thing” that can be captured and labled. Preach Tony Preach
I have written over 214 articles on “trust” over the past 12 years. I have read endless books and done countless presentations on the topic of TRUST. I have always searched for the relationships between trust and strategy, value, consent, privacy, identity, data and risk. The well-reasoned articles include Imaging a Digital Strategy starting from TRUST, Trust is not a destination!, How can Brands restore user trust?, A segmentation model based on trust, The relationship between Trust, Risk and Privacy. This article brings together some of the thinking already explored in previous articles but as the new drawing below.
How to unleash the full potential of data? Alan Mitchell
The main reason why vital information is not getting where it needs to be is that our data economy has evolved to be an organisation-centric ‘One User One Use’ (OUOU) system — whereas, thanks to the inner logic of data itself, it needs to operate as a ‘Many Users, Many Uses’ (MUMU) data ecosystem.
Self Sovereign Identity
Identity at Microsoft Ignite: Strengthening Zero Trust defenses in the era of hybrid work
I’m happy to share that Azure AD verifiable credentials is entering preview in just a few weeks. Developers will get an SDK, with quick-start guides, for building apps that request and verify credentials, just like they do with usernames and passwords.
Microsoft's Dream of Decentralized IDs Enters the Real World
Think of the platform as a digital wallet like Apple Pay or Google Pay, but for identifiers rather than credit cards. Microsoft is starting with things like university transcripts, diplomas, and professional credentials, letting you add them to its Microsoft Authenticator app along with two-factor codes.
IATA app (by Evernym) makes CNN Travel
"Governments decide the requirements to travel; airlines and passengers need to comply," says the IATA on its website, emphasizing that the airline body is not itself mandating that passengers must have a Covid-19 vaccine in order to travel.
DIF Monthly Newsletter
There’s tons of great updates in this months DIF newsletter, we can’t cover it all.
Sidetree Spec V1.0.0 Working Group approved status
Wallet Security WG kickoff and next steps
There was a meeting working to refine the charter, last Monday, and another meeting on the same topic this Monday March 8 at 6PM CET. Register here and join the dedicated mailing list.
Africa Discussion Group Kick-off Call!
The group will connect companies, projects, and organizations involved in identity, credential, and trust technologies in the African economic zone.
It will also drive the African regional participation in technical and professional organizations typically dominated by Europe and North America.
Mailing list • Kick-off Call March 4th, 8 AM (GMT)
Verifiable Credentials Issuance Blockster
When an issuer creates a verifiable credential, it contains following information
Who has issued – DID of the Issuer
To whom it is issued – User Identifier
Attributes of the credential – Details of the credential being Issued
When it is Issued – Date of issuance
Credential proof with Issuer signature that makes it tamper evident
Revocation details
Announcing Pico Engine 1.0 Windley
provides a more modular design that better supports future enhancements and allows picos to be less dependent on a specific engine for operation.
Building Decentralized Applications with Pico Networks
The Role of Witness Organizations in Verifiable Credentials
The basis is that not every source of a verifiable credential has an interest in issuing verifiable credentials and that it is not only logical but beneficial to the ecosystem of trust that witness organizations will issue on behalf of these sources.
Witness orgs sit in layer 3 of the Trust Over IP stack as authoritative issuers. Witness orgs are to VCs like Dunn and Bradstreet (D&B) is to the finance world: they issue claims as a recognized authority.
The Digital Product Passport: Tracking Data Throughout the Entire Lifecycle.
In the real estate industry, TRUST&TRACE can be used by companies to obtain required compliance information from a network of participating companies. In this way, all property data is collected step by step: from building construction and leasing to sale and demolition.
Decentralized Identity with the Tezos DID Method
Spruce and TQ Tezos are jointly releasing the draft specification and initial implementation of Decentralized Identifiers (DIDs) based on the Tezos blockchain.
Letter to the Biden Administration Reached its Intended Audience - CCI
Last week, LFPH/CCI was invited to brief the Office of the National Coordinator for Health Information Technology (ONC), located within the Office of the Secretary for the U.S. Department of Health and Human Services (HHS).
attended by 15 ONC staff including the National Coordinator and Deputy National Coordinator. Brian Behlendorf, Executive Director of Linux Foundation Public Health (LFPH), introduced LFPH and CCI and provided an overview of our approach and key progress so far. Jenny Wanger (Director of Programs at LFPH), Lucy Yang, John Walker, and Kaliya Young supported the Q&A where we were asked about implementation timeline, interoperability challenges, vaccine data sources, patient identity management, etc.
New Series by Evernym
Part 0: The 7 Deadly Sins of Digital Customer Relationships
Part 1: Decentralized Identifiers: Building Smarter, More Sustainable Customer Relationships
DIDs are about building lasting private and secure digital relationships with customers, and as we’ll see with each of the Deadly Sins, about reducing costs, increasing compliance and enabling truly personalized products and services – without being creepy.
Part 2: How DIDs Can Enable True Customer Centricity
By using Decentralized Identifiers (DIDs) – creating a unique identifier for each and every different relationship – customers can seamlessly set up a new, highly secure, two-way channel with the business
An Introduction to the Trinsic Wallet
When an organization requests information from an end user, the end user can decide whether to accept or reject the request. If the request is accepted, the wallet will find the relevant data from all of their credentials that is needed to fulfill the request.
City of Austin dabbling in SSI
Many folks within the identity space see VC infrastructure as the future of identification. If much of our online identity is reputation based, then VCs represent a formal method for linking reputations and vouching for others to form a web of trust within which individuals are able to conduct identity transactions in a less centralized way.
Time for governments to get serious about digital identities by Deloitte
While the tools may already exist to solve the government’s identity crisis, real progress will only be made if governments significantly evolve their legacy approaches to digital identity.
Identity Not SSI
Second Version of W3C WebAuthn advances to Proposed Recommendation (PR)
(W3C) has published this Proposed Recommendation (PR) for the Web Authentication (WebAuthn) Level 2 specification, bringing the second version of WebAuthn one step closer to becoming a completed standard. […] this second version adds additional features, among them for user verification enhancements, manageability, enterprise features, and an Apple attestation format.
OpenID Foundation Announces Increases to Membership Dues in 2021
The Foundation cannot exist without the ongoing support of both long-standing and new members alike so the board of directors would like to thank all members and those considering membership for their support
Utah State Legislature Passes Facial Recognition Bill
allows public agencies to use facial recognition as long as certain guidelines are followed. Most notably, law enforcement officers must submit a written request before performing a facial recognition search, and must be able to provide a valid reason for doing so.
OIDC for Identity Assurance (eKYC & IDA) Enables 30 Million+ Bank Customers to ID with Third Parties
Enhanced Due Diligence How to do it Right
Both CDD and EDD are part of a complete KYC process. Identity verification (IDV) at the account-opening stage is one of the most critical moments in the process, but it doesn’t end there: read on to identify when your due diligence should kick up a notch.
FATF and Global Crytpto Regulatory News
The Financial Action Task Force (FATF) held its winter Plenary session on 22nd, 24th, and 25th February and welcomed over 205 delegates to its third virtual conference since the start of the pandemic.
Single Sign-on vs. Federated IDM : Complete Guide
OAuth Patterns and Anti-Patterns - a DZone Refcard
This five-page reference guide covers the latest in OAuth and clarifies some common misunderstandings of applying it to real world use cases. With a focus on OAuth 2.0, OpenID Connect, and best practices